Which four actions should you perform in sequence?
Your network contains an Active Directory domain named contoso.com.
The domain contains two servers named Server1 and Server2 that run Windows Server 2016.
You need to install Microsoft Advanced Threat Analytics (ATA) on Server1 and Server2.
Which four actions should you perform in sequence?
Build List and Reorder:
Which Group Policy setting or settings should you configure?
Your network contains an Active Directory domain named contoso.com. The domain contains a server named
Server1.
On Server1, administrators plan to use several scripts that have the .ps1 extension.
You need to ensure that when code is generated from the scripts, an event containing the details of the code is
logged in the Operational log.
Which Group Policy setting or settings should you configure?
What should you install on Server1 first?
You have a server named Server1 that runs Windows Server 2016.
You need to install Security Compliance Manager (SCM) 4.0 on Server1.
What should you install on Server1 first?
You need to retrieve the password of the Administrator …
Your network contains an Active Directory domain named contoso.com. The domain contains a server named
Server1 that runs Windows Server 2016.
The local administrator credentials of Server1 are managed by using the Local Administrator Password Solution
(LAPS).
You need to retrieve the password of the Administrator account on Server1. What should you do?
Which cmdlet should you use?
You have a server named Server1 that runs Windows Server 2016.
You configure Just Enough Administration (JEA) on Server1.
You need to view a list of commands that will be available to a user named User1 when User1 establishes a
JEA session to Server1.
Which cmdlet should you use?
You need to view which script blocks were executed by u…
You enable and configure PowerShell Script Block Logging.
You need to view which script blocks were executed by using Windows PowerShell scripts.
What should you do?
Does this meet the goal?
Your network contains an Active Directory domain named contoso.com. All client computers run Windows 10.
You plan to deploy a Remote Desktop connection solution for the client computers.
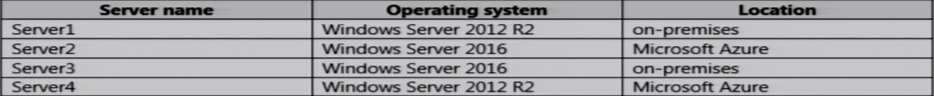
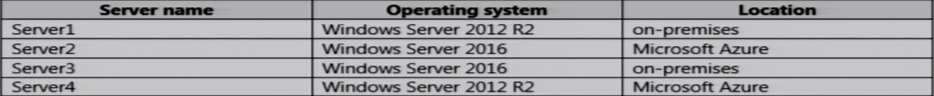
You have four available servers in the domain that can be configured as Remote Desktop servers. The servers
are configured as shown in the following table.
You need to ensure that all Remote Desktop connections can be protected by using Remote Credential Guard.
Solution: You deploy the Remote Desktop connection solution by using Server4.
Does this meet the goal?
Does this meet the goal?
Your network contains an Active Directory domain named contoso.com. All client computers run Windows 10.
You plan to deploy a Remote Desktop connection solution for the client computers.
You have four available servers in the domain that can be configured as Remote Desktop servers. The servers
are configured as shown in the following table.
You need to ensure that all Remote Desktop connections can be protected by using Remote Credential Guard.
Solution: You deploy the Remote Desktop connection solution by using Server3.
Does this meet the goal?
Solution: You configure an inbound rule that allows the…
Your network contains an Active Directory domain named contoso.com.
The domain contains a computer named Computer1 that runs Windows 10.
The network uses the 172.16.0.0/16 address space.
Computer1 has an application named App1.exe that is located in D:\\Apps\\.
App1.exe is configured to accept connections on TCP port 8080.
You need to ensure that App1.exe can accept connections only when Computer1 is connected to the corporate
network.
Solution: You configure an inbound rule that allows the TCP protocol on port 8080 and applies to all profiles
Does this meet the goal?
Does this meet the goal?
Your network contains an Active Directory domain named contoso.com.
The domain contains a computer named Computer1 that runs Windows 10.
The network uses the 172.16.0.0/16 address space.
Computer1 has an application named App1.exe that is located in D:\\Apps\\.
App1.exe is configured to accept connections on TCP port 8080.
You need to ensure that App1.exe can accept connections only when Computer1 is connected to the corporate
network.
Solution: You configure an inbound rule that allows the TCP protocol on port 8080, uses a scope of
172.16.0.0/16 for local IP addresses, and applies to a private
profile.
Does this meet the goal?