Choose the columns on which a PRIMARY KEY constraint needs to be created to accomplish this.
You work as a Database Developer for GraySoft Inc. You are designing a database to record
information about potential customers. You create a table named ProductInquiry for the database.
The table is given below:
You want to uniquely identify the product in which a customer is interested. Choose the columns on
which a PRIMARY KEY constraint needs to
be created to accomplish this.
Which of the following is the process of extracting trails on a regular basis so that they can be transferred
Which of the following is the process of extracting trails on a regular basis so that they can be
transferred to a designated security system where the database administrators do not have access?
What should you do?
You manage a large database named Sales. The Sales database contains a table named OrderDetails,
which is a heavily transacted table with frequent inserts. Indexes in the table often become
fragmented due to excessive page splitting. You want to minimize the amount of fragmentation due
to page splits. What should you do?
Which of the following steps will you take to accomplish the task?
You are the database administrator of a MySQL server that runs on a Windows server. All clients are
local clients. For security, you want to disable connections from the remote clients. Which of the
following steps will you take to accomplish the task?
Identify the most appropriate ER-diagram that represents the relationship between department and employees
Consider the case of an organization having many departments. Each department has a department
head known as senior manager. Several employees are working in a department under the senior
manager. Identify the most appropriate ER-diagram that represents the relationship between
department and employees.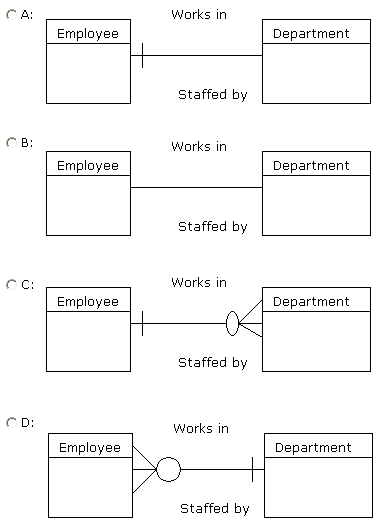
Which of the following statements is true about referential integrity?
Which of the following statements is true about referential integrity?
Which of the following are DML commands?
Which of the following are DML commands? Each correct answer represents a complete solution.
Choose all that apply.
Which of the following commands can be used to change the authorization type in DB2 9?
Which of the following commands can be used to change the authorization type in DB2 9? Each
correct answer represents a complete solution. Choose all that apply.
Which of the following database planning steps will help him to accomplish the task?
Smith works as a Database Administrator for DWorlds Inc. The management instructs him to plan a
database where identifying the key objects or entities for database management is important.
Which of the following database planning steps will help him to accomplish the task?
What code will create the trigger to meet your goals?
You are a database developer for a database named Customers hosted on a SQL Server 2008 server.
Recently, several customers were deleted from the Customers database. To ensure this is not
repeated in future, you have decided to create a DML trigger to prevent it. What code will create the
trigger to meet your goals? Each correct answer represents a complete solution. Choose all that
apply.

