What should you configure?
Your network contains two DNS servers named DNS1 and DNS2 that run Windows Server 2012 R2.
DNS1 has a primary zone named contoso.com. DNS2 has a secondary copy of the contoso.com zone.
You need to log the zone transfer packets sent between DNS1 and DNS2.
What should you configure?
You need to configure the adatum.com zone to support Na…
Your network contains an Active Directory domain named contoso.com.
The domain contains a domain controller named DC1 that runs Windows Server 2012 R2.
DC1 has the DNS Server server role installed.
The network contains client computers that run either Linux, Windows 7, or Windows 8.
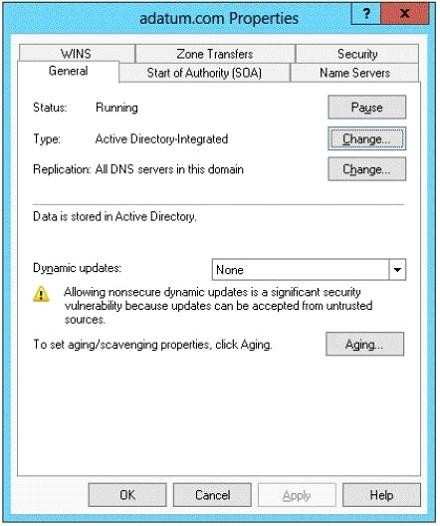
You have a zone named adatum.com as shown in the exhibit. (Click the Exhibit button.)
You plan to configure Name Protection on all of the DHCP servers.
You need to configure the adatum.com zone to support Name Protection.
What should you do?
Which tool should you use?
Your network contains an Active Directory forest named contoso.com.
The forest contains a single domain. The forest functional level is Windows Server 2012 R2.
You have a domain controller named DC1. On DC1, you create a new Group Policy object (GPO) named GPO1.
You need to verify that GPO1 was replicated to all of the domain controllers.
Which tool should you use?
You need to ensure that the new RODC will be able to re…
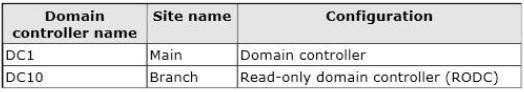
Your network contains an Active Directory domain named contoso.com.
All domain controllers run Windows Server 2012 R2. The domain contains two domain controllers.
The domain controllers are configured as shown in the following table.
The Branch site contains a perimeter network.
For security reasons, client computers in the perimeter network can communicate with client computers in the Branch site only.
You plan to deploy a new RODC to the perimeter network in the Branch site.
You need to ensure that the new RODC will be able to replicate from DC10.
What should you do first on DC10?
Which type of trust policy should you create?
Your network contains an Active Directory forest named adatum.com.
The forest contains an Active Directory Rights Management Services (AD RMS) cluster.
A partner company has an Active Directory forest named litwareinc.com.
The partner company does not have AD RMS deployed.
You need to ensure that users in litwareinc.com can consume rights-protected content from adatum.com.
Which type of trust policy should you create?
You need to ensure that the Include all folders that st…
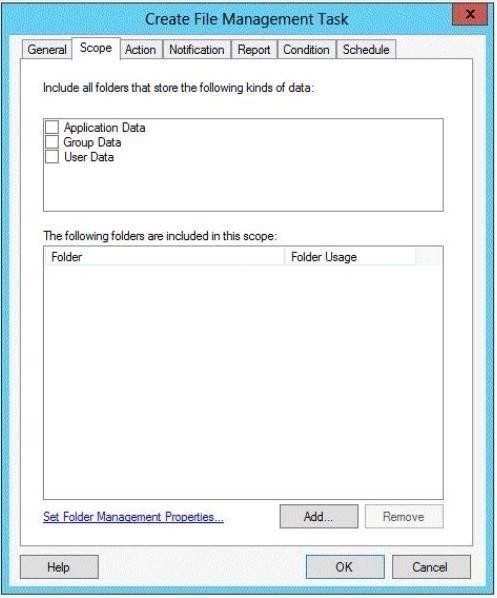
You have a server named Server1 that runs Windows Server 2012 R2.
Server1 has the File Server Resource Manager role service installed.
You are creating a file management task as shown in the exhibit. (Click the Exhibit button.)
You need to ensure that the Include all folders that store the following kinds of data list displays an entry named Corporate Data.
What should you do?
What should you identify?
Your network contains a perimeter network and an internal network.
The internal network contains an Active Directory Federation Services (AD FS) 2.1 infrastructure.
The infrastructure uses Active Directory as the attribute store.
You plan to deploy a federation server proxy to a server named Server2 in the perimeter network.
You need to identify which value must be included in the certificate that is deployed to Server2.
What should you identify?
What should you identify?
Your network contains a perimeter network and an internal network.
The internal network contains an Active Directory Federation Services (AD FS) 2.1 infrastructure.
The infrastructure uses Active Directory as the attribute store.
You plan to deploy a federation server proxy to a server named Server2 in the perimeter network.
You need to identify which value must be included in the certificate that is deployed to Server2.
What should you identify?
Which command should you run?
Your network contains an Active Directory domain named contoso.com.
The domain contains a file server named File1 that runs a Server Core Installation of Windows Server 2012 R2.
File1 has a volume named D that contains home folders. File1 creates a shadow copy of volume D twice a day.
You discover that volume D is almost full.
You add a new volume named H to File1.
You need to ensure that the shadow copies of volume D are stored on volume H.
Which command should you run?
You need to ensure that the virtual machines on Server1…
Your network contains an Active Directory domain named contoso.com.
The domain contains two servers named Server1 and Server2 that run Windows Server 2012 R2.
Server1 is a file server that has the Hyper-V server role installed. Server1 hosts several virtual machines.
The virtual machine configuration files are stored on drive D and the VHD files are stored on drive E.
You plan to replace drive E with a larger volume. You need to ensure that the virtual machines on Server1 remain available while drive E is being replaced.
What should you do?