Which two configurations should you perform from DNS Manager?
Your network contains an Active Directory domain named contoso.com. The domain
contains a domain controller named DC1 that runs Windows Server 2012 R2. DC1 has the
DNS Server server role installed.
The network contains client computers that run either Linux, Windows 7, or Windows 8.
You have a standard primary zone named adatum.com as shown in the exhibit. (Click the
Exhibit button.)
You plan to configure Name Protection on all of the DHCP servers.
You need to configure the adatum.com zone to support Name Protection.
Which two configurations should you perform from DNS Manager? (Each correct answer
presents part of the solution. Choose two.)
What Windows PowerShell cmdlet should you run on Server1?
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain
contains two servers named Server1 and Server2. All servers run Windows Server 2012 R2.
You install the DHCP Server server role on both servers.
On Server1, you have the DHCP scope configured as shown in the exhibit. (Click the Exhibit
button.)
You need to configure the scope to be load-balanced across Server1 and Server2.
What Windows PowerShell cmdlet should you run on Server1?
To answer, select the appropriate options in the answer area.
You need to ensure that the IP-PBX can route calls successfully to the Exchange Server 2013 organization
###BeginCaseStudy###
Case Study: 3
Contoso Ltd
Overview
General Overview
Contoso, Ltd., is an aerospace engineering company that manufactures jet engine
parts for various industries and government agencies. Contoso has an Exchange
Server 2013 organization.
A partner company named Tailspin Toys has an Exchange Server 2010
organization.
Physical Locations
Contoso has two offices. The offices are located in Montreal and Chicago.
Each office contains a data center:
The Montreal and Chicago offices connect to each other by using a direct WAN link.
All connections to the Internet are routed through the Montreal office.
Most of Contoso’s employees work from the Montreal office.
Existing Environment
The network of Contoso is configured as shown in the exhibit. (Click the Exhibit
button.)
The network of Contoso contains the following components:
Client computers that run either Microsoft Outlook 2007 or Outlook 2010.
Users who have a primary SMTP address that uses the contoso.com suffix.
A retention policy that retains all email messages for 580 days and is associated to
all users.
Six servers that have Exchange Server installed. The servers are configured as
shown in the following table.
A data availability group (DAG) named DAG1 that contains all of the mailbox
servers. EX5 is configured as the witness server for DAG1. A file server in the
Chicago office is configured as an alternate witness server. DAG1 has Datacenter
Activation Coordination (DAC) mode enabled.
Requirements
Planned Changes
Contoso plans to implement the following changes:
Implement an organization relationship between Contoso and Tailspin Toys.
Move the mailboxes of all the members of the sales department to Office 365.
Evaluate Unified Messaging (UM) by conducting a small pilot in the Montreal office.
Security Requirements
Contoso identifies the following security requirements:
Ensure that the data in the Exchange Server databases cannot be read if a hard disk
is stolen.
Prevent temporary employees from executing a Reply All or a Forward of any email
messages they receive.
Prevent temporary contractors from changing the configurations of the user accounts
for the users in the research and development department.
Ensure that all of the connections to Outlook Web App from the Internet use
Extensible Authentication Protocol (EAP) protocols and Transport Layer Security
(TLS) protocols.
Secure all of the email messages from the users at Tailspin Toys to the Contoso
users. Ensure that all of the messages can be secured if the certificates at Tailspin
Toys are issued by a trusted third-party certification authority (CA).
Auditing Requirements
Contoso identifies the following requirements for auditing mailboxes:
The manager of the legal department must receive a daily report by email that
contains a record of all the eDiscovery mailbox searches.
Any access to a mailbox by a service account must be excluded from the daily
report.
Compliance Requirements
All of the email messages in the Sent Items folder of each user in the marketing
department of Contoso must be deleted automatically after 365 days.
Office 365 Coexistence Requirements
Contoso identifies the following Office 365 coexistence requirements:
Office 365 users must be able to access their mailbox by using their Active Directory
user account in Contoso.
On-premises users must be able to share free/busy information and calendar
information with the Office 365 users.
###EndCaseStudy###
You implement the UM pilot. You capture and analyze a network trace from the IP-PBX. You discover
that SIP/MTLS requests for TCP 5061 to EX1 are dropped. You need to ensure that the IP-PBX can
route calls successfully to the Exchange Server 2013 organization.
What should you do?
What Windows PowerShell cmdlet should you run?
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain
contains two DHCP servers named Server1 and Server2. Both servers have multiple IPv4
scopes.
Server1 and Server2 are used to assign IP addresses for the network IDs of 172.20.0.0/16
and 131.107.0.0/16.
You install the IP Address Management (IPAM) Server feature on a server named IPAM1
and configure IPAM1 to manage Server1 and Server2.
Some users from the 172.20.0.0 network report that they occasionally receive an IP address
conflict error message.
You need to identify whether any scopes in the 172.20.0.0 network ID conflict with one
another.
What Windows PowerShell cmdlet should you run?
To answer, select the appropriate options in the answer area.
What should you configure?
Your network contains two DNS servers named DN51 and DNS2 that run Windows Server
2012 R2.
DNS1 has a primary zone named contoso.com. DNS2 has a secondary copy of the
contoso.com zone.
You need to log the zone transfer packets sent between DNS1 and DNS2.
What should you configure?
Which two tasks should you recommend?
###BeginCaseStudy###
Case Study: 3
Contoso Ltd
Overview
General Overview
Contoso, Ltd., is an aerospace engineering company that manufactures jet engine
parts for various industries and government agencies. Contoso has an Exchange
Server 2013 organization.
A partner company named Tailspin Toys has an Exchange Server 2010
organization.
Physical Locations
Contoso has two offices. The offices are located in Montreal and Chicago.
Each office contains a data center:
The Montreal and Chicago offices connect to each other by using a direct WAN link.
All connections to the Internet are routed through the Montreal office.
Most of Contoso’s employees work from the Montreal office.
Existing Environment
The network of Contoso is configured as shown in the exhibit. (Click the Exhibit
button.)
The network of Contoso contains the following components:
Client computers that run either Microsoft Outlook 2007 or Outlook 2010.
Users who have a primary SMTP address that uses the contoso.com suffix.
A retention policy that retains all email messages for 580 days and is associated to
all users.
Six servers that have Exchange Server installed. The servers are configured as
shown in the following table.
A data availability group (DAG) named DAG1 that contains all of the mailbox
servers. EX5 is configured as the witness server for DAG1. A file server in the
Chicago office is configured as an alternate witness server. DAG1 has Datacenter
Activation Coordination (DAC) mode enabled.
Requirements
Planned Changes
Contoso plans to implement the following changes:
Implement an organization relationship between Contoso and Tailspin Toys.
Move the mailboxes of all the members of the sales department to Office 365.
Evaluate Unified Messaging (UM) by conducting a small pilot in the Montreal office.
Security Requirements
Contoso identifies the following security requirements:
Ensure that the data in the Exchange Server databases cannot be read if a hard disk
is stolen.
Prevent temporary employees from executing a Reply All or a Forward of any email
messages they receive.
Prevent temporary contractors from changing the configurations of the user accounts
for the users in the research and development department.
Ensure that all of the connections to Outlook Web App from the Internet use
Extensible Authentication Protocol (EAP) protocols and Transport Layer Security
(TLS) protocols.
Secure all of the email messages from the users at Tailspin Toys to the Contoso
users. Ensure that all of the messages can be secured if the certificates at Tailspin
Toys are issued by a trusted third-party certification authority (CA).
Auditing Requirements
Contoso identifies the following requirements for auditing mailboxes:
The manager of the legal department must receive a daily report by email that
contains a record of all the eDiscovery mailbox searches.
Any access to a mailbox by a service account must be excluded from the daily
report.
Compliance Requirements
All of the email messages in the Sent Items folder of each user in the marketing
department of Contoso must be deleted automatically after 365 days.
Office 365 Coexistence Requirements
Contoso identifies the following Office 365 coexistence requirements:
Office 365 users must be able to access their mailbox by using their Active Directory
user account in Contoso.
On-premises users must be able to share free/busy information and calendar
information with the Office 365 users.
###EndCaseStudy###
You need to recommend which tasks must be performed to meet the security requirements for
Tailspin Toys.
Which two tasks should you recommend? (Each correct answer presents part of the solution.
Choose two.)
Which three actions should you perform?
###BeginCaseStudy###
Case Study: 3
Contoso Ltd
Overview
General Overview
Contoso, Ltd., is an aerospace engineering company that manufactures jet engine
parts for various industries and government agencies. Contoso has an Exchange
Server 2013 organization.
A partner company named Tailspin Toys has an Exchange Server 2010
organization.
Physical Locations
Contoso has two offices. The offices are located in Montreal and Chicago.
Each office contains a data center:
The Montreal and Chicago offices connect to each other by using a direct WAN link.
All connections to the Internet are routed through the Montreal office.
Most of Contoso’s employees work from the Montreal office.
Existing Environment
The network of Contoso is configured as shown in the exhibit. (Click the Exhibit
button.)
The network of Contoso contains the following components:
Client computers that run either Microsoft Outlook 2007 or Outlook 2010.
Users who have a primary SMTP address that uses the contoso.com suffix.
A retention policy that retains all email messages for 580 days and is associated to
all users.
Six servers that have Exchange Server installed. The servers are configured as
shown in the following table.
A data availability group (DAG) named DAG1 that contains all of the mailbox
servers. EX5 is configured as the witness server for DAG1. A file server in the
Chicago office is configured as an alternate witness server. DAG1 has Datacenter
Activation Coordination (DAC) mode enabled.
Requirements
Planned Changes
Contoso plans to implement the following changes:
Implement an organization relationship between Contoso and Tailspin Toys.
Move the mailboxes of all the members of the sales department to Office 365.
Evaluate Unified Messaging (UM) by conducting a small pilot in the Montreal office.
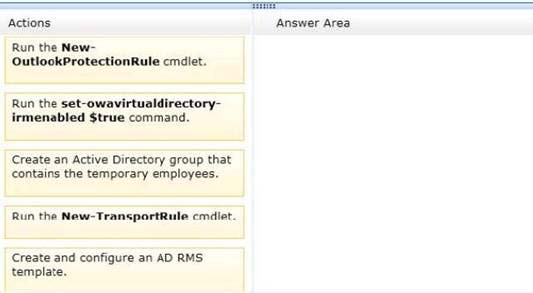
Security Requirements
Contoso identifies the following security requirements:
Ensure that the data in the Exchange Server databases cannot be read if a hard disk
is stolen.
Prevent temporary employees from executing a Reply All or a Forward of any email
messages they receive.
Prevent temporary contractors from changing the configurations of the user accounts
for the users in the research and development department.
Ensure that all of the connections to Outlook Web App from the Internet use
Extensible Authentication Protocol (EAP) protocols and Transport Layer Security
(TLS) protocols.
Secure all of the email messages from the users at Tailspin Toys to the Contoso
users. Ensure that all of the messages can be secured if the certificates at Tailspin
Toys are issued by a trusted third-party certification authority (CA).
Auditing Requirements
Contoso identifies the following requirements for auditing mailboxes:
The manager of the legal department must receive a daily report by email that
contains a record of all the eDiscovery mailbox searches.
Any access to a mailbox by a service account must be excluded from the daily
report.
Compliance Requirements
All of the email messages in the Sent Items folder of each user in the marketing
department of Contoso must be deleted automatically after 365 days.
Office 365 Coexistence Requirements
Contoso identifies the following Office 365 coexistence requirements:
Office 365 users must be able to access their mailbox by using their Active Directory
user account in Contoso.
On-premises users must be able to share free/busy information and calendar
information with the Office 365 users.
###EndCaseStudy###
DRAG DROP
The Montreal data center experiences a power failure. You need to ensure that all the users can
access their mailbox. Which three actions should you perform? To answer, move the three
appropriate actions from the list of actions to the answer area and arrange them in the correct
order.
You need to ensure that your DNS servers can resolve partners.adatum.com to the correct IP address immediately
Your network contains an Active Directory forest named contoso.com.
Users frequently access the website of an external partner company. The URL of the
website is http://partners.adatum.com.
The partner company informs you that it will perform maintenance on its Web server and that
the IP addresses of the Web server will change.
After the change is complete, the users on your internal network report that they fail to
access the website. However, some users who work from home report that they can access
the website.
You need to ensure that your DNS servers can resolve partners.adatum.com to the correct
IP address immediately.
What should you do?
Which command should you include in the recommendation?
###BeginCaseStudy###
Case Study: 4
Trey Research
Overview
General Overview
Trey Research is a brokerage firm that has 5,000 users. Trey Research has a
finance department, a human resources department, an investment department, and
a legal department.
Trey Research is acquiring a partner company named Fabrikam, Inc.
Physical Locations
Trey Research has four main offices located in Boston, Chicago, New York, and
Atlanta.
The offices connect to each other by using a WAN link. The Chicago office connects
directly to the Internet.
Existing Environment
Network Environment
Trey Research has an Active Directory forest named treyresearch.com. The forest
contains a single domain. All domain controllers run Windows Server 2012.
Each office is configured as an Active Directory site.
All user accounts are in an organizational unit (OU) based on their department. All
users are in a universal security group based on their department.
Trey Research has a Lync Server 2013 infrastructure. The infrastructure is
configured to required encryption for voice traffic.
Exchange Server Organization
Trey Research has an Exchange Server organization that contains five servers. The
servers are configured as shown in the following table.
The mailbox databases are mounted on the Exchange servers shown in the
following table.
All of the mailboxes of the users in the executives department are mounted on DB3.
A public folder database named PF1 is mounted on EX5.
The Exchange Server organization has the following configurations:
Users in the legal department use a shared mailbox named Legal. Legal is enabled
for In-Place Hold. Legal is the only mailbox on DB2.
All inbound and outbound email messages to and from the Internet are routed
through EX1.
Email messages sent and received by Fabrikam are secured by using Mutual TLS.
All public folders are stored in PF1.
All users connect to their mailbox by using Microsoft Outlook 2013 and Outlook Web
App.
Fabrikam has an Exchange Server 2013 organization.
Problem Statements
Trey Research identifies the following issues:
After a change to a certificate, users report that email messages sent to Fabrikam
are not delivered.
The storage for DB3 fails. The storage will be offline for the next two days.
Requirements
Planned Changes
Trey Research plans to implement the following changes:
Move all public folders to an Exchange Server 2013 server. The solution must
ensure that all users cannot modify the public folders stored on EX5 after the
planned move.
Integrate Unified Messaging (UM) services with the Lync Server 2013 infrastructure.
Collaboration Requirements
Custom recipient MailTips created in the Exchange Server organization of Trey
Research must be visible to the users at Fabrikam. The solution must ensure that
administrators can define a subset of users who can share their MailTips.
Auditing Requirements
The following actions must be audited for actions in the Legal mailbox only:
Delegate – Purge mailbox content
Delegate – Transfer file between folders
Administrator – Messages sent by administrator
Administrator – Open any content within the mailbox
Security Requirements
Trey Research identifies the following security requirements:
Ensure that the users in the finance department can protect email messages from
being altered in transit, regardless of the recipient.
Prevent the email messages sent to the users in the human resources department
from being forwarded to external recipients.
Prevent the audio files in voice mail message marked as Private from being
extracted from email messages.
Redirect email messages that contain social security information to the legal
department.
Compliance Requirements
Trey Research identifies the following compliance requirements:
All users must be notified before they send an email message that contains any five
bank account numbers to an external recipient. The users must be able to override
the requirement if they have a valid business reason to send the email message.
Users must use a custom message classification when they send email messages
that contain information about the planned acquisition of Fabrikam.
1 Only the users in the legal department must be able to use eDiscovery to view the
contents of email messages sent by the finance department users.
###EndCaseStudy###
HOTSPOT
You need to recommend a solution that meets the auditing requirements.
Which command should you include in the recommendation? (To answer, select the appropriate
options in the answer area.)
Which three actions should you perform?
###BeginCaseStudy###
Case Study: 3
Contoso Ltd
Overview
General Overview
Contoso, Ltd., is an aerospace engineering company that manufactures jet engine
parts for various industries and government agencies. Contoso has an Exchange
Server 2013 organization.
A partner company named Tailspin Toys has an Exchange Server 2010
organization.
Physical Locations
Contoso has two offices. The offices are located in Montreal and Chicago.
Each office contains a data center:
The Montreal and Chicago offices connect to each other by using a direct WAN link.
All connections to the Internet are routed through the Montreal office.
Most of Contoso’s employees work from the Montreal office.
Existing Environment
The network of Contoso is configured as shown in the exhibit. (Click the Exhibit
button.)
The network of Contoso contains the following components:
Client computers that run either Microsoft Outlook 2007 or Outlook 2010.
Users who have a primary SMTP address that uses the contoso.com suffix.
A retention policy that retains all email messages for 580 days and is associated to
all users.
Six servers that have Exchange Server installed. The servers are configured as
shown in the following table.
A data availability group (DAG) named DAG1 that contains all of the mailbox
servers. EX5 is configured as the witness server for DAG1. A file server in the
Chicago office is configured as an alternate witness server. DAG1 has Datacenter
Activation Coordination (DAC) mode enabled.
Requirements
Planned Changes
Contoso plans to implement the following changes:
Implement an organization relationship between Contoso and Tailspin Toys.
Move the mailboxes of all the members of the sales department to Office 365.
Evaluate Unified Messaging (UM) by conducting a small pilot in the Montreal office.
Security Requirements
Contoso identifies the following security requirements:
Ensure that the data in the Exchange Server databases cannot be read if a hard disk
is stolen.
Prevent temporary employees from executing a Reply All or a Forward of any email
messages they receive.
Prevent temporary contractors from changing the configurations of the user accounts
for the users in the research and development department.
Ensure that all of the connections to Outlook Web App from the Internet use
Extensible Authentication Protocol (EAP) protocols and Transport Layer Security
(TLS) protocols.
Secure all of the email messages from the users at Tailspin Toys to the Contoso
users. Ensure that all of the messages can be secured if the certificates at Tailspin
Toys are issued by a trusted third-party certification authority (CA).
Auditing Requirements
Contoso identifies the following requirements for auditing mailboxes:
The manager of the legal department must receive a daily report by email that
contains a record of all the eDiscovery mailbox searches.
Any access to a mailbox by a service account must be excluded from the daily
report.
Compliance Requirements
All of the email messages in the Sent Items folder of each user in the marketing
department of Contoso must be deleted automatically after 365 days.
Office 365 Coexistence Requirements
Contoso identifies the following Office 365 coexistence requirements:
Office 365 users must be able to access their mailbox by using their Active Directory
user account in Contoso.
On-premises users must be able to share free/busy information and calendar
information with the Office 365 users.
###EndCaseStudy###
DRAG DROP
You need to implement a solution to meet the security requirement for the temporary employees.
You deploy an Active Directory Rights Management Services (AD RMS) cluster, and then you run the
Set-IRMConfiguration cmdlet.
Which three actions should you perform?
To answer, move the three appropriate actions from the list of actions to the answer area and
arrange them in the correct order.