Which two statements are true as they relate to a sniffer mode IDP sensor deployment?
Which two statements are true as they relate to a sniffer mode IDP sensor deployment? (Choose
two.)
what does the sensor do?
If an IDP sensor finds that a packet matchesa particular IDP rule, and then finds a matching exempt
rule, what does the sensor do?
Which three actions must be taken prior to deploying an IDP sensor (in transparent mode) in a network?
Which three actions must be taken prior to deploying an IDP sensor (in transparent mode) in a
network?
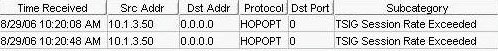
which rule base would have generated the log message?
What is "a unique pattern that always exists within an attack"?
What is “a unique pattern that always exists within an attack”?
Which sensor command can be used to determine if profiler data is being sent to Security Manager?
Which sensor command can be used to determine if profiler data is being sent to Security Manager?
Which three statements are true as they relate to a transparent mode IDP deployment?
Which three statements are true as they relate to a transparent mode IDP deployment? (Choose
three.)
Which sensor process handles all communication between the sensor and Security Manager?
Which sensor process handles all communication between the sensor and Security Manager?
Which three columns can be seen in the Application View of the Enterprise Security Profiler?
Which three columns can be seen in the Application View of the Enterprise Security Profiler?
(Choose three.)
what is a permitted object?
In Enterprise Security Profiler (ESP), what is a permitted object?