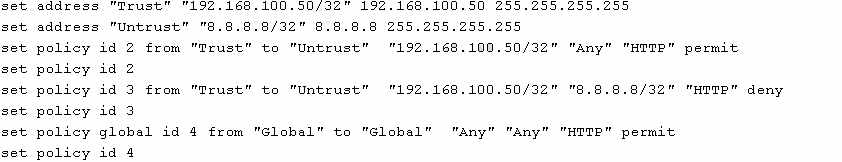
what happens to this traffic?
Network traffic with a source IP of 192.168.100.60, destination IP of 8.8.8.8, and a destination port
of 80 is sent through the ScreenOS device. The inbound zone is Trust, the outbound zone is
Untrust.
Based on the policy configuration shown in the exhibit, what happens to this traffic?
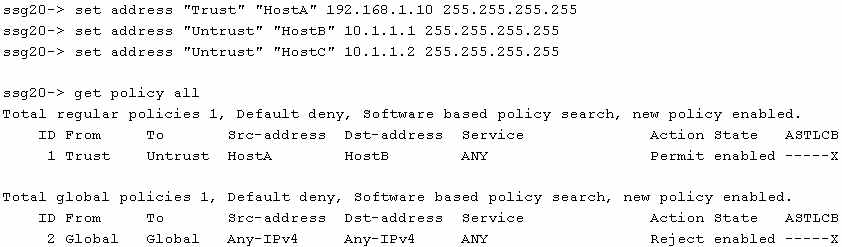
which two statements are correct?
What is causing the traffic problem?
— Exhibit –ssg20-> set address “Trust” “192.168.1.0/32” 10.20.1.0 255.255.255.0
ssg20-> set address “Untrust” “10.204.1.0/24” 10.204.1.0 255.255.255.0
ssg20-> set address “Untrust” “192.168.1.0/24” 192.168.1.0 255.255.255.255
ssg20-> get policy id 1
name:”none” (id 1), zone Trust -> Untrust,action Permit, status “enabled”
src “192.168.1.0/32”, dst “192.168.1.0/24”, serv “FTP”
Rules on this VPN policy: 0
nat off, Web filtering : disabled
vpn unknown vpn, policy flag 00000000, session backup: on, idle reset: on
traffic shaping off, scheduler n/a, serv flag 00
log no, log count 0, alert no, counter no(0) byte rate(sec/min) 0/0
total octets 0, counter(session/packet/octet) 0/0/0
priority 7, diffserv marking Off
tadapter: state off, gbw/mbw 0/0 policing (no)
No Authentication
No User, User Group or Group expression set
— Exhibit –FTP connections from host 10.20.1.10 to server 192.168.1.100 are not working. You produce the
output shown in the exhibit. What is causing the traffic problem?
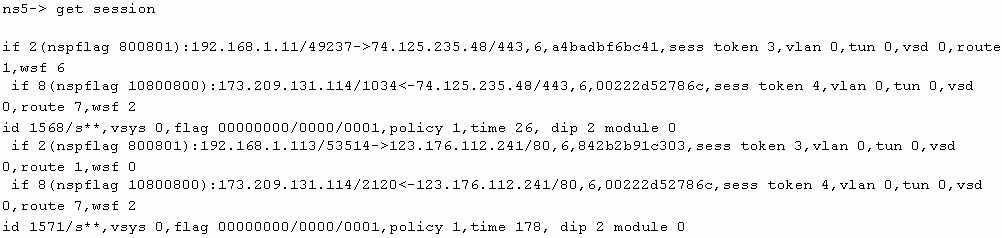
Which statement is correct?
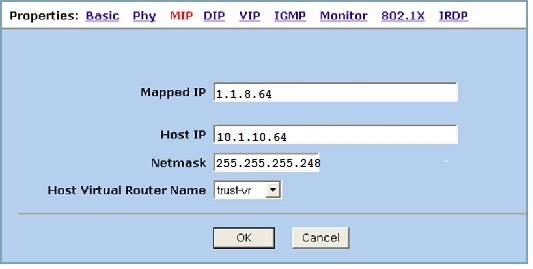
What would you use to configure this behavior?
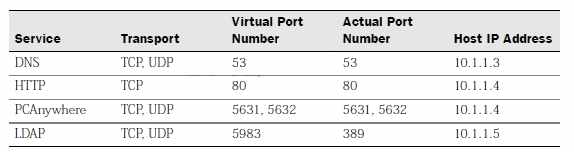
In the network shown in the exhibit, you have been asked to enable users in the Untrust zone to
contact Server1 on TCP port 80 using IP address 1.1.1.1. You also need to allow Server1 to make
connections to hosts in the Untrust zone. When Server1 makes connections to the Untrust zone,
the source address of its traffic should be translated to 1.1.1.1.
What would you use to configure this behavior?
Which command would you use to accomplish this task?
— Exhibit –ssg5(M)-> get conf | incl ethernet1/2
set interface “ethernet1/2” zone “Untrust”
set interface ethernet1/2 ip 10.0.0.1/24
set interface ethernet1/2 route
set interface “ethernet1/2” description “Internet Connection 1”
set interface ethernet1/2 ip manageable
set interface ethernet1/2 manage ping
— Exhibit –You need to add a DIP pool to the interface shown in the exhibit. The DIP pool has been assigned
the IP addresses 20.20.20.1 through 20.20.20.10.
Which command would you use to accomplish this task?
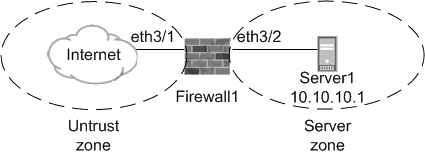
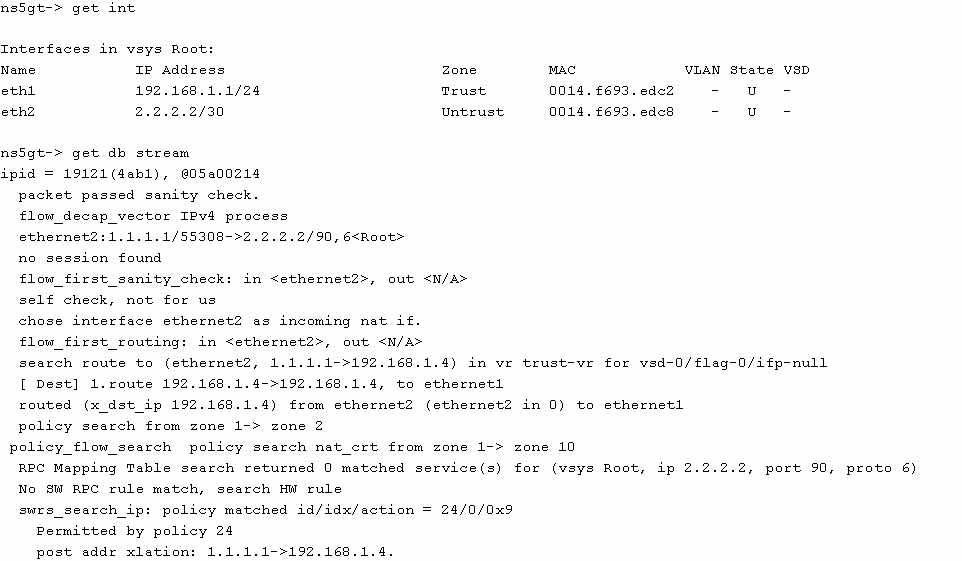
which NAT configuration is being used?
— Exhibit –ns5gt-> get int
Interfaces in vsys Root:
Name IP Address Zone MAC VLAN State VSD
eth1 192.168.1.1/24 Trust 0014.f693.edc2 – U –
eth2 2.2.2.2/30 Untrust 0014.f693.edc8 – U –
ns5gt-> get db stream
****** .0: <Trust/ethernet1> packet received [69]******
ipid = 22281(5709), @059ff214
packet passed sanity check.
flow_decap_vector IPv4 process
ethernet1:192.168.1.102/52380->4.2.2.2/53,17<Root>
no session found
flow_first_sanity_check: in <ethernet1>, out <N/A>
chose interface ethernet1 as incoming nat if.
flow_first_routing: in <ethernet1>, out <N/A>
search route to (ethernet1, 192.168.1.102->4.2.2.2) in vr trust-vr for vsd-0/flag-0/ifp-null
[ Dest] 7.route 4.2.2.2->2.2.2.1, to ethernet2
routed (x_dst_ip 4.2.2.2) from ethernet1 (ethernet1 in 0) to ethernet2
Permitted by policy 1
dip id = 2, 192.168.1.102/52380->2.2.2.2/2157
choose interface ethernet2 as outgoing phy if
no loop on ifp ethernet2.
routed (x_dst_ip 4.2.2.2) from ethernet1 (ethernet1 in 0) to ethernet2
policy search from zone 2-> zone 1
— Exhibit –Referring to the debug output shown in the exhibit, which NAT configuration is being used?