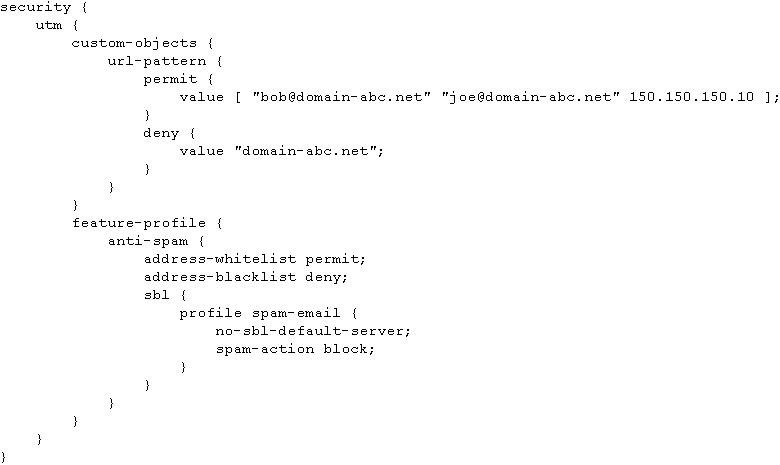
what happens when an e-mail message arrives at the SRX device from mary@domain-abc.net at IP address 150.150.1
Which statement is correct?
what happens when a user attempts to send a zip file through the SRX device using FTP?
— Exhibit —
[edit security utm feature-profile content-filtering]
user@host# show
profile profileA {
block-content-type {
exe;
zip;
}
notification-options {
type message;
custom-message “Not permitted. illegal file type”;
}
}
— Exhibit —
Click the Exhibit button.
Your SRX Series device includes the content filtering configuration shown in the exhibit.
Assuming the content filtering profile has been properly applied, what happens when a user
attempts to send a zip file through the SRX device using FTP?
what happens when a user attempts to access the Web site www.juniper.net through the SRX device?
— Exhibit —
[edit security utm]
user@host# show
custom-objects {
url-pattern {
permit {
value http://www.domain-abc.net;
}
deny {
value http://www.domain-abc.net/movies;
}
}
custom-url-category {
whitelist {
value permit;
}
blacklist {
value deny;
}
}
}
feature-profile {
web-filtering {
url-whitelist whitelist;
url-blacklist blacklist;
type juniper-local;
juniper-local {
profile profileA {
default block;
custom-block-message “Website access not permitted”;
}
}
}
}
— Exhibit —
Click the Exhibit button.
Your SRX Series device includes the Web filtering configuration shown in the exhibit.
Assuming the Web filtering profile has been properly applied, what happens when a user
attempts to access the Web site www.juniper.net through the SRX device?
What does a zone contain?
What does a zone contain?
which two statements are correct?
Referring to the exhibit, which two statements are correct? (choose two)
[edit security zones] user@host#show security-zone untrust {
screen untrust-screen
host-inbound-traffic {
system-services
{ ssh; ping;
}}
Interfaces {
ge-0/0/1.0
ge-0/0/3.0{ host-inboun
d-traffic{ protocols {
ospf; } } }
Which statement is true about a logical interface?
Which statement is true about a logical interface?
Which step must you perform before committing a configuration with the policy?
You want to configure a security policy that allows traffic to a particular host.
Which step must you perform before committing a configuration with the policy?
Which three match criteria must each security policy include?
Which three match criteria must each security policy include? (Choose three.)
Which three IP option fields can an attacker exploit to cause problems in a network?
Which three IP option fields can an attacker exploit to cause problems in a network?
(Choose three.)