Which of the following cryptographic systems is MOST ap…
Which of the following cryptographic systems is MOST appropriate for bulk data encryption and
small devices such as smart cards?
An efficient use of public key infrastructure (PKI) sho…
An efficient use of public key infrastructure (PKI) should encrypt the:
Which of the following ensures a sender’s authenticity …
Which of the following ensures a sender’s authenticity and an e-mail’s confidentiality?
To detect attack attempts that the firewall is unable t…
Which of the following should be a concern to an IS aud…
Which of the following should be a concern to an IS auditor reviewing a wireless network?
what aspect of an authorized honeypot?
An IS auditor should be MOST concerned with what aspect of an authorized honeypot?
The FIRST action triggered by the IDS should be to:
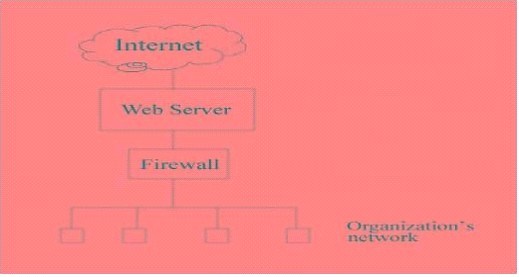
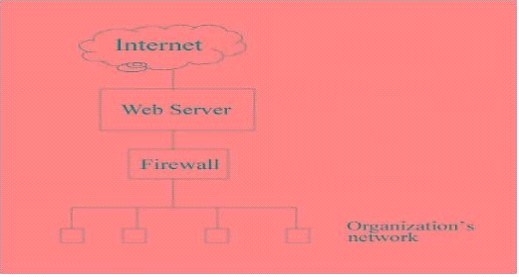
E-mail traffic from the Internet is routed via firewall-1 to the mail gateway. Mail is routed from the
mail gateway, via firewall-2, to the mail recipients in the internal network. Other traffic is not allowed.
For example, the firewalls do not allow direct traffic from the Internet to the internal network.
The intrusion detection system (IDS) detects traffic for the internal network that did not originate
from the mail gateway. The FIRST action triggered by the IDS should be to:
Which of the following is a distinctive feature of the …
Which of the following is a distinctive feature of the Secure Electronic Transactions (SET) protocol
when used for electronic credit card payments?
The role of the certificate authority (CA) as a third p…
The role of the certificate authority (CA) as a third party is to:
The PRIMARY objective of Secure Sockets Layer (SSL) is …
The PRIMARY objective of Secure Sockets Layer (SSL) is to ensure: