What authorization is needed to use the AUDIT statement…
What authorization is needed to use the AUDIT statement to create an audit policy?
What authority must be held to create a trusted context?
What authority must be held to create a trusted context?
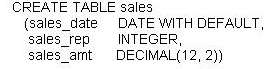
what must be done to protect the table as desired?
What type of Label-Based Access Control (LBAC) security…
What type of Label-Based Access Control (LBAC) security label component is used to define a scale in which
the first element listed represents the highest level of trust a person can have and the last element listed
represents the lowest level of trust a person can have?
Which is a valid statement about the Row and Column Acc…
Which is a valid statement about the Row and Column Access Control (RCAC) feature?
What authority is required to grant a user ACCESSCTRL a…
What authority is required to grant a user ACCESSCTRL authority?
Which administrative authority is needed to grant ACCES…
Which administrative authority is needed to grant ACCESSCTRL, DATAACCESS, or SECADM authority to
other users, groups, or roles?
Which statement regarding SECADM authority is true?
Which statement regarding SECADM authority is true?
Which High Availability Disaster Recovery (HADR) synchr…
Which High Availability Disaster Recovery (HADR) synchronization mode provides the shortest transaction
response time but has the highest probability of transaction losses if the primary system fails?
Which statement is NOT true about a database restore op…
Which statement is NOT true about a database restore operation?