Which two requirements are addressed by implementing IBM Tivoli Identity Manager?
Which two requirements are addressed by implementing IBM Tivoli Identity Manager? (Choose
two.)
Which three corresponding security requirements can be addressed by IBM Tivoli Federated Identity Manager?
As you analyze a customer business processes, you focus on a subset dealing with crossenterprise Web transactions, both HTML- and SOAP-based. Which three corresponding security
requirements can be addressed by IBM Tivoli Federated Identity Manager? (Choose three.)
Which encryption method is used by IBM Tivoli Access Manager for e-business (ITAMeb) when ITAMeb is configured
Which encryption method is used by IBM Tivoli Access Manager for e-business (ITAMeb) when
ITAMeb is configured with the FIPS mode enabled?
Which two security requirements are addressed by IBM Tivoli Access Manager for e-business?
Which two security requirements are addressed by IBM Tivoli Access Manager for e-business?
(Choose two.)
what advantage does the certification bring to IBM?
When the “Open Group” certifies an IBM product, what advantage does the certification bring to
IBM?
What is the primary security requirement indicated by the customer statement?
In a conversation about business requirements, a customer states:
We are going through the latest big initiative right now. The focus is on time to market with new,
bigger and better Web-based business applications. We have no time for implementing stronger
security and we do not see how you can help us with this.” What is the primary security
requirement indicated by the customer statement?
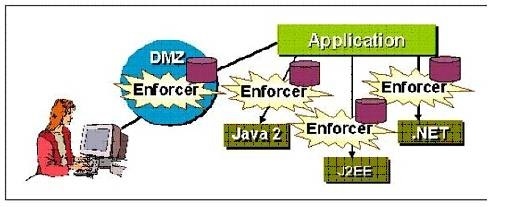
Which security scenario is indicated by the word "Enforcer" that appears several times in the exhibi
Which protocol was developed jointly by IBM, Microsoft, and VeriSign?
Which protocol was developed jointly by IBM, Microsoft, and VeriSign?
Which term is used to denote such a system?
A business-partner of IBM, specializing in security products, is interested in setting up a specific
system configured to simulate a few common network services. They want to intentionally leave it
exposed to the external network access, in order to attract would-be attackers and study their
attack patterns. Which term is used to denote such a system?
What should you do to help the customer achieve this?
A current IBM Tivoli Access Manager for e-business customer wants to add the ability to provide
services to a third-party company employees. The customer does not want to create accounts and
manage passwords for the third-party company employees. What should you do to help the
customer achieve this?