Even though F5 is an application delivery controller, i…
Even though F5 is an application delivery controller, it can also effectively mitigate attacks directed at the network layer.
service can incorporate dynamic lists of threatening IP…
Complete the statement below by choosing the correct word or phrase to complete the sentence.
By identifying IP addresses and security categories associated with malicious activity, the BIG-IP………….. service can incorporate dynamic lists of threatening IP
addresses into the BIG-IP platform, adding context to policy decisions.
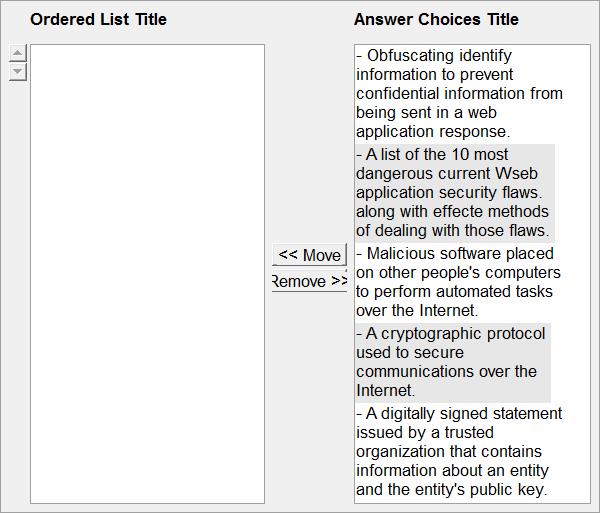
Content scrubbing Build List and Reorder:
What are the other consequences to a business as a resu…
When a business is hacked, they often lose more than money. What are the other consequences to a business as a result of being hacked?
Select two.
Select the key question you would use to ask your custo…
Select the key question you would use to ask your customer related to DNS attacks?
What feature of the F5 Exchange solution helps administ…
What feature of the F5 Exchange solution helps administrators to streamline implementation for added security and granular control?
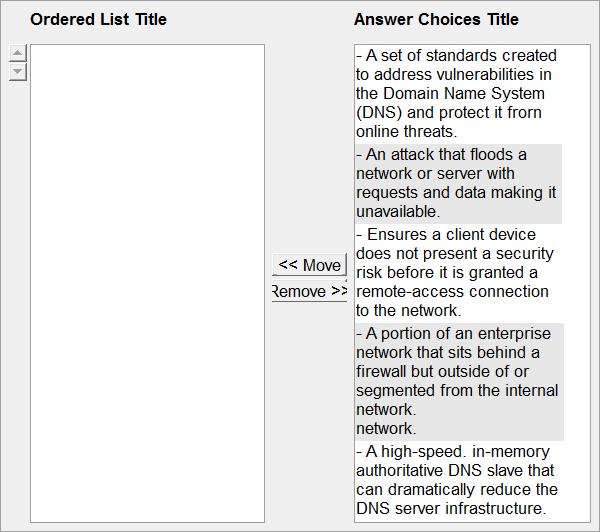
Endpoint inspection Build List and Reorder:
Which two of the following statements about how TMOS ty…
Which two of the following statements about how TMOS typically manages traffic between a client and server are accurate?
which additional IP addresses will the BIG-IP system change?
When using SNAT, which additional IP addresses will the BIG-IP system change? Select two.
True or false? All members of a pool must share the sam…
True or false? All members of a pool must share the same service port?