Using Internet logging software to investigate a case of malicious use of computers, the investigator comesacross some entries that appear odd.
From the log, the investigator can see where the person in question went on the Internet. From the log, it
appears that the user was manually typing in different user ID numbers. What technique this user was trying?

A.
Parameter tampering
B.
Cross site scripting
C.
SQL injection
D.
Cookie Poisoning


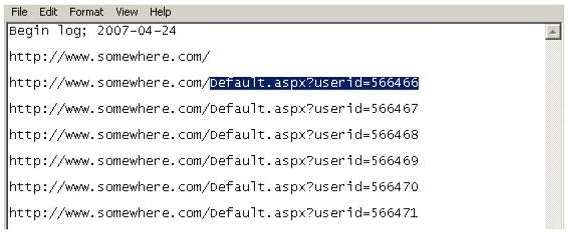
Parameter tampering is a form of Web-based attack in which certain parameters in the URL or Web page form field data entered by a user are changed without that user’s authorization.