What is the maximum drive size supported?
FAT32 is a 32-bit version of FAT file system using smaller clusters and results in efficient storage
capacity. What is the maximum drive size supported?
which step of the computer forensics investigation methodology would you run MD5 checksum on the evidence?
In which step of the computer forensics investigation methodology would you run MD5 checksum on the
evidence?
Network forensics allows Investigators 10 inspect network traffic and logs to identify and locate the attack s
Network forensics allows Investigators 10 inspect network traffic and logs to identify and locate the
attack system Network forensics can reveal: (Select three answers)
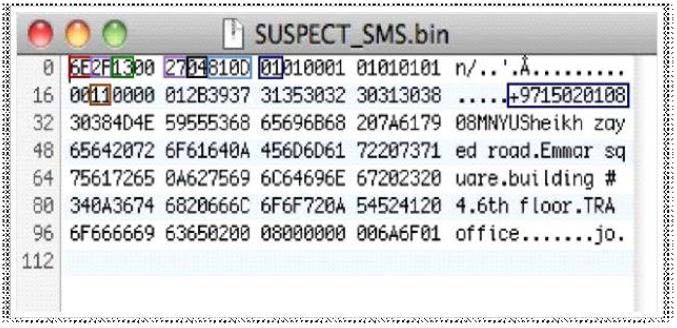
Determine the message length from following hex viewer record:
Which of the following protocols works under the transport layer of TCP/IP?
TCP/IP (Transmission Control Protocol/Internet Protocol) is a communication protocol used to connect
different hosts in the Internet. It contains four layers, namely the network interface layer. Internet layer,
transport layer, and application layer. Which of the following protocols works under the transport layer of
TCP/IP?
Which of the following statements does not support the case assessment?
Which of the following statements does not support the case assessment?
What happens when a file is deleted in windows7?
File deletion is a way of removing a file from a computer’s file system. What happens when a file is
deleted in windows7?
Which of the following wireless access control attacks allows the attacker…?
Wireless access control attacks aim to penetrate a network by evading WLAN access control measures,
such as AP MAC filters and Wi-Fi port access controls. Which of the following wireless access control
attacks allows the attacker to set up a rogue access point outside the corporate perimeter, and then lure
the employees of the organization to connect to it?
What is cold boot (hard boot)?
What is cold boot (hard boot)?
If the INF02 file is deleted, it is re-created when you___________.
When a file or folder is deleted, the complete path, including the original file name, is stored in a special
hidden file called “INF02” in the Recycled folder. If the INF02 file is deleted, it is re-created when
you___________.