what is the definition of a Wrapper?
In the context of Trojans, what is the definition of a Wrapper?
Which step would you perform to detect this type of Trojan?
Which type of hacker represents the highest risk to your network?
Which type of hacker represents the highest risk to your network?
What type of insider threat would Shayla be considered?
Shayla is an IT security consultant, specializing in social engineering and external penetration
tests. Shayla has been hired on by Treks Avionics, a subcontractor for the Department of Defense.
Shayla has been given authority to perform any and all tests necessary to audit the company’s
network security.
No employees for the company, other than the IT director, know about Shayla’s work she will be
doing. Shayla’s first step is to obtain a list of employees through company website contact pages.
Then she befriends a female employee of the company through an online chat website. After
meeting with the female employee numerous times, Shayla is able to gain her trust and they
become friends. One day, Shayla steals the employee’s access badge and uses it to gain
unauthorized access to the Treks Avionics offices.
What type of insider threat would Shayla be considered?
What port number is used by Kerberos protocol?
What port number is used by Kerberos protocol?
What does FIN in TCP flag define?
What does FIN in TCP flag define?
Why do you think this is possible?
Annie has just succeeded in stealing a secure cookie via a XSS attack. She is able to replay the
cookie even while the session is invalid on the server. Why do you think this is possible?
This attack technique is used when a Web application is vulnerable to an SQL Injection but the results of the
This attack technique is used when a Web application is vulnerable to an SQL Injection but the
results of the Injection are not visible to the attacker.
How do you ensure if the e-mail is authentic and sent from fedex.com?
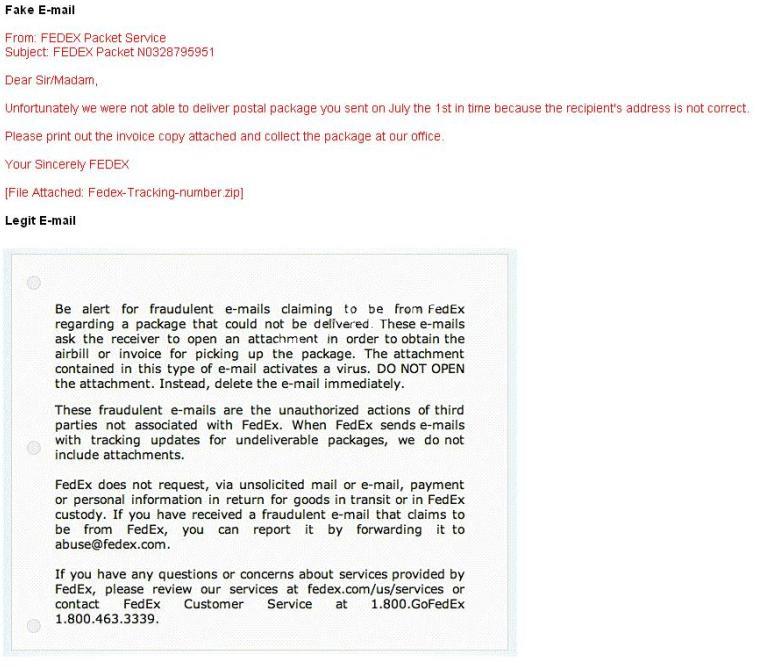
A common technique for luring e-mail users into opening virus-launching attachments is to send
messages that would appear to be relevant or important to many of their potential recipients. One
way of accomplishing this feat is to make the virus-carrying messages appear to come from some
type of business entity retailing sites, UPS, FEDEX, CITIBANK or a major provider of a common
service.
Here is a fraudulent e-mail claiming to be from FedEx regarding a package that could not be
delivered. This mail asks the receiver to open an attachment in order to obtain the FEDEX tracking
number for picking up the package. The attachment contained in this type of e-mail activates a
virus.
Vendors send e-mails like this to their customers advising them not to open any files attached with
the mail, as they do not include attachments.
Fraudulent e-mail and legit e-mail that arrives in your inbox contain the fedex.com as the sender of
the mail.
How do you ensure if the e-mail is authentic and sent from fedex.com?
What file system vulnerability does the following command take advantage of?
What file system vulnerability does the following command take advantage of?
type c:\anyfile.exe > c:\winnt\system32\calc.exe:anyfile.exe