How do you prevent DNS spoofing?
Let’s imagine three companies (A, B and C), all competing in a challenging global environment.
Company A and B are working together in developing a product that will generate a major
competitive advantage for them. Company A has a secure DNS server while company B has a
DNS server vulnerable to spoofing. With a spoofing attack on the DNS server of company B,
company C gains access to outgoing e-mails from company B. How do you prevent DNS
spoofing? (Select the Best Answer.)
What built-in Windows feature could you have implemented to protect the sensitive information on these laptops
You are the CIO for Avantes Finance International, a global finance company based in Geneva.
You are responsible for network functions and logical security throughout the entire corporation.
Your company has over 250 servers running Windows Server, 5000 workstations running
Windows Vista, and 200 mobile users working from laptops on Windows 7.
Last week, 10 of your company’s laptops were stolen from salesmen while at a conference in
Amsterdam. These laptops contained proprietary company information. While doing damage
assessment on the possible public relations nightmare this may become, a news story leaks about
the stolen laptops and also that sensitive information from those computers was posted to a blog
online.
What built-in Windows feature could you have implemented to protect the sensitive information on
these laptops?
Which DNS resource record can indicate how long any "DNS poisoning" could last?
Which DNS resource record can indicate how long any “DNS poisoning” could last?
What is Rogue security software?
A Trojan horse is a destructive program that masquerades as a benign application. The software
initially appears to perform a desirable function for the user prior to installation and/or execution,
but in addition to the expected function steals information or harms the system.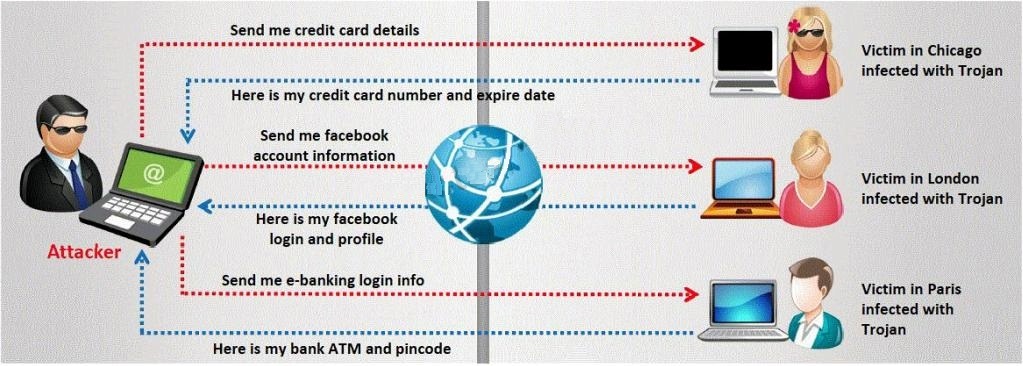
The challenge for an attacker is to send a convincing file attachment to the victim, which gets
easily executed on the victim machine without raising any suspicion. Today’s end users are quite
knowledgeable about malwares and viruses. Instead of sending games and fun executables,
Hackers today are quite successful in spreading the Trojans using Rogue security software.
What is Rogue security software?
How did the attacker accomplish this hack?
Joseph was the Web site administrator for the Mason Insurance in New York, who’s main Web
site was located at www.masonins.com. Joseph uses his laptop computer regularly to administer
the Web site.
One night, Joseph received an urgent phone call from his friend, Smith. According to Smith, the
main Mason Insurance web site had been vandalized! All of its normal content was removed and
replaced with an attacker’s message ”Hacker Message: You are dead! Freaks!
From his office, which was directly connected to Mason Insurance’s internal network, Joseph
surfed to the Web site using his laptop. In his browser, the Web site looked completely intact. No
changes were apparent. Joseph called a friend of his at his home to help troubleshoot the
problem. The Web site appeared defaced when his friend visited using his DSL connection. So,
while Smith and his friend could see the defaced page, Joseph saw the intact Mason Insurance
web site. To help make sense of this problem, Joseph decided to access the Web site using his
dial-up ISP. He disconnected his laptop from the corporate internal network and used his modem
to dial up the same ISP used by Smith.
After his modem connected, he quickly typed www.masonins.com in his browser to reveal the
following web page:
H@cker Mess@ge:
Y0u @re De@d! Fre@ks!
After seeing the defaced Web site, he disconnected his dial-up line, reconnected to the internal
network, and used Secure Shell (SSH) to log in directly to the Web server. He ran Tripwire against
the entire Web site, and determined that every system file and all the Web content on the server
were intact.
How did the attacker accomplish this hack?
Which of the following is NOT part of CEH Scanning Methodology?
Which of the following is NOT part of CEH Scanning Methodology?
Which of the following tools are used for enumeration?
Which of the following tools are used for enumeration? (Choose three.)
What is Lee seeing here?
Lee is using Wireshark to log traffic on his network. He notices a number of packets being directed
to an internal IP from an outside IP where the packets are ICMP and their size is around 65, 536
bytes. What is Lee seeing here?
What did the following commands determine?
What did the following commands determine?
C: user2sid \earth guest
S-1-5-21-343818398-789336058-1343024091-501
C:sid2user 5 21 343818398 789336058 1343024091 500
Name is Joe
Domain is EARTH
What is it called?
This method is used to determine the Operating system and version running on a remote target
system. What is it called?

