Once the relevant information is extracted, the tokens are placed back on the network to gain access.
However, host A can continue to receive data as long as the SYN sequence numbers of transmitted packets from h
The FIN flag is set and sent from host A to host B when host A has no more data to transmit
(Closing a TCP connection). This flag releases the connection resources. However, host A can
continue to receive data as long as the SYN sequence numbers of transmitted packets from host
B are lower than the packet segment containing the set FIN flag.
Which of the following hping2 command is responsible for the above snort alert?
Jason is the network administrator of Spears Technology. He has enabled SNORT IDS to detect
attacks going through his network. He receives Snort SMS alerts on his iPhone whenever there is
an attempted intrusion to his network.
He receives the following SMS message during the weekend.
An attacker Chew Siew sitting in Beijing, China had just launched a remote scan on Jason’s
network with the hping command.
Which of the following hping2 command is responsible for the above snort alert?
What Google search will accomplish this?
Leesa is the senior security analyst for a publicly traded company. The IT department recently
rolled out an intranet for company use only with information ranging from training, to holiday
schedules, to human resources data. Leesa wants to make sure the site is not accessible from
outside and she also wants to ensure the site is Sarbanes-Oxley (SOX) compliant. Leesa goes to
a public library as she wants to do some Google searching to verify whether the company’s
intranet is accessible from outside and has been indexed by Google. Leesa wants to search for a
website title of “intranet” with part of the URL containing the word “intranet” and the words “human
resources” somewhere in the webpage.
What Google search will accomplish this?
What is the first character that Bob should use to attempt breaking valid SQL request?
Bob has been hired to do a web application security test. Bob notices that the site is dynamic and
must make use of a back end database. Bob wants to see if SQL Injection would be possible.
What is the first character that Bob should use to attempt breaking valid SQL request?
How was Bill able to get Internet access without using an agency laptop?
Hampton is the senior security analyst for the city of Columbus in Ohio. His primary responsibility
is to ensure that all physical and logical aspects of the city’s computer network are secure from all
angles. Bill is an IT technician that works with Hampton in the same IT department. Bill’s primary
responsibility is to keep PC’s and servers up to date and to keep track of all the agency laptops
that the company owns and lends out to its employees. After Bill setup a wireless network for the
agency, Hampton made sure that everything was secure. He instituted encryption, rotating keys,
turned off SSID broadcasting, and enabled MAC filtering. According to agency policy, only
company laptops are allowed to use the wireless network, so Hampton entered all the MAC
addresses for those laptops into the wireless security utility so that only those laptops should be
able to access the wireless network.
Hampton does not keep track of all the laptops, but he is pretty certain that the agency only
purchases Dell laptops. Hampton is curious about this because he notices Bill working on a
Toshiba laptop one day and saw that he was on the Internet. Instead of jumping to conclusions,
Hampton decides to talk to Bill’s boss and see if they had purchased a Toshiba laptop instead of
the usual Dell. Bill’s boss said no, so now Hampton is very curious to see how Bill is accessing the
Internet. Hampton does site surveys every couple of days, and has yet to see any outside wireless
network signals inside the company’s building.
How was Bill able to get Internet access without using an agency laptop?
If the password is 7 characters or less, than the second half of the hash is always:
LAN Manager Passwords are concatenated to 14 bytes, and split in half. The two halves are
hashed individually. If the password is 7 characters or less, than the second half of the hash is
always:
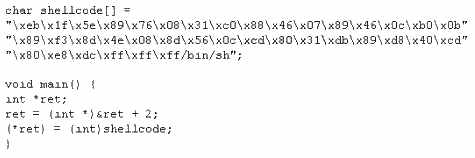
When writing shellcodes, you must avoid ____________ because these will end the string.
Why Jess is not picking up hashes .from the network?
Jess the hacker runs L0phtCrack’s built-in sniffer utility that grabs SMB password hashes and
stores them for offline cracking. Once cracked, these passwords can provide easy access to
whatever network resources the user account has access to. But Jess is not picking up hashes
from the network. Why?
Why did the 14 character passwords not take much longer to crack than the 8 character passwords?
Harold works for Jacobson Unlimited in the IT department as the security manager. Harold has
created a security policy requiring all employees to use complex 14 character passwords.
Unfortunately, the members of management do not want to have to use such long complicated
passwords so they tell Harold’s boss this new password policy should not apply to them. To
comply with the management’s wishes, the IT department creates another Windows domain and
moves all the management users to that domain. This new domain has a password policy only
requiring 8 characters.
Harold is concerned about having to accommodate the managers, but cannot do anything about it.
Harold is also concerned about using LanManager security on his network instead of NTLM or
NTLMv2, but the many legacy applications on the network prevent using the more secure NTLM
and NTLMv2. Harold pulls the SAM files from the DC’s on the original domain and the new domain
using Pwdump6.
Harold uses the password cracking software John the Ripper to crack users’ passwords to make
sure they are strong enough. Harold expects that the users’ passwords in the original domain will
take much longer to crack than the management’s passwords in the new domain. After running the
software, Harold discovers that the 14 character passwords only took a short time longer to crack
than the 8 character passwords.
Why did the 14 character passwords not take much longer to crack than the 8 character
passwords?