Which forensic investigating concept trails the whole i…
Which forensic investigating concept trails the whole incident from how the attack began to how the victim was
affected?
what layer of the OSI model are you monitoring while wa…
You have been called in to help with an investigation of an alleged network intrusion. After questioning the
members of the company IT department, you search through the server log files to find any trace of the
intrusion. After that you decide to telnet into one of the company routers to see if there is any evidence to be
found. While connected to the router, you see some unusual activity and believe that the attackers are currently
connected to that router. You start up an ethereal session to begin capturing traffic on the router that could be
used in the investigation. At what layer of the OSI model are you monitoring while watching traffic to and from
the router?
How many exits should Steven include in his design for …
Steven has been given the task of designing a computer forensics lab for the company he works for. He has
found documentation on all aspects of how to design a lab except the number of exits needed. How many exits
should Steven include in his design for the computer forensics lab?
What type of removable media could the investigator use?
A forensics investigator needs to copy data from a computer to some type of removable media so he can
examine the information at another location. The problem is that the data is around 42GB in size. What type of
removable media could the investigator use?
What crime should Julie focus on?
Julie is a college student majoring in Information Systems and Computer Science. She is currently writing an
essay for her computer crimes class. Julie paper focuses on white-collar crimes in America and how forensics
investigators investigate the cases. Julie would like to focus the subject. Julie would like to focus the subject of
the essay on the most common type of crime found in corporate America. What crime should Julie focus on?
What type of flash memory card comes in either Type I o…
What type of flash memory card comes in either Type I or Type II and consumes only five percent of the power
required by small hard drives?
what do the 0.0.0.0 IP addresses signify?
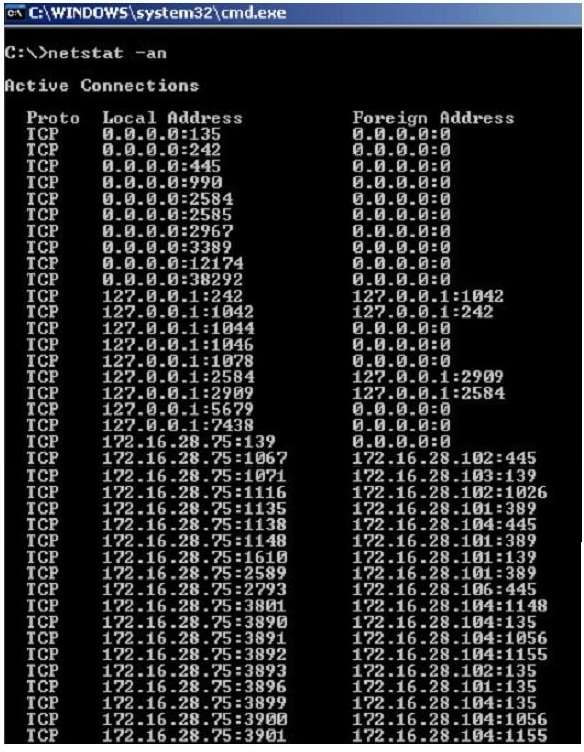
Jack Smith is a forensics investigator who works for Mason Computer Investigation Services. He is
investigating a computer that was infected by Ramen Virus.
He runs the netstat command on the machine to see its current connections. In the following screenshot, what
do the 0.0.0.0 IP addresses signify?
what should be searched to find a JPEG file in hexadeci…
When searching through file headers for picture file formats, what should be searched to find a JPEG file in
hexadecimal format?
When the case is brought to court, whom should the pros…
Davidson Trucking is a small transportation company that has three local offices in Detroit Michigan. Ten
female employees that work for the company have gone to an attorney reporting that male employees
repeatedly harassed them and that management did nothing to stop the problem. Davidson has employee
policies that outline all company guidelines, including awareness on harassment and how it will not be
tolerated. When the case is brought to court, whom should the prosecuting attorney call upon for not upholding
company policy?
what layer does a cross site scripting attack occur on?
At what layer does a cross site scripting attack occur on?