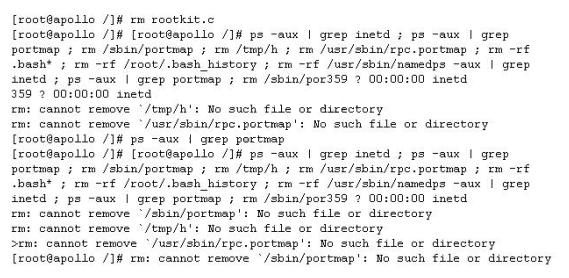
What is the hacker trying to accomplish here?
Which of the following statements best describes the term Vulnerability?
Which of the following statements best describes the term Vulnerability?
What has Blake just accomplished?
Blake is in charge of securing all 20 of his company’s servers. He has enabled hardware and
software firewalls, hardened the operating systems, and disabled all unnecessary services on all
the servers. Unfortunately, there is proprietary AS400 emulation software that must run on one of
the servers that requires the telnet service to function properly. Blake is especially concerned
about this since telnet can be a very large security risk in an organization. Blake is concerned
about how this particular server might look to an outside attacker so he decides to perform some
footprinting, scanning, and penetration tests on the server. Blake telnets into the server using Port
80 and types in the following command:
HEAD / HTTP/1.0
After pressing enter twice, Blake gets the following results: What has Blake just accomplished?
Which of the following web browser can adequately fill this purpose?
Bob is a very security conscious computer user. He plans to test a site that is known to have
malicious applets, code, and more. Bob always make use of a basic Web Browser to perform such
testing.
Which of the following web browser can adequately fill this purpose?
What must be enabled in SQL Server to launch these attacks?
You want to perform advanced SQL Injection attack against a vulnerable website. You are unable
to perform command shell hacks on this server. What must be enabled in SQL Server to launch
these attacks?
How much information will Clive obtain from the client before commencing his test?
Clive has been hired to perform a Black-Box test by one of his clients.
How much information will Clive obtain from the client before commencing his test?
Who is considered an insider?
A majority of attacks come from insiders, people who have direct access to a company’s computer
system as part of their job function or a business relationship. Who is considered an insider?
What is Kevin attempting hereto gain access to Katy’s mailbox?
Kevin is an IT security analyst working for Emerson Time Makers, a watch manufacturing
company in Miami. Kevin and his girlfriend Katy recently broke up after a big fight. Kevin believes
that she was seeing another person. Kevin, who has an online email account that he uses for most
of his mail, knows that Katy has an account with that same company. Kevin logs into his email
account online and gets the following URL after successfully logged in:
http://www.youremailhere.com/mail.asp?mailbox=Kevin&Smith=121%22 Kevin changes the URL
to: http://www.youremailhere.com/mail.asp?mailbox=Katy&Sanchez=121%22 Kevin is trying to
access her email account to see if he can find out any information. What is Kevin attempting here
to gain access to Katy’s mailbox?
What would be the best method to accurately identify the services running on a victim host?
Scanning for services is an easy job for Bob as there are so many tools available from the
Internet. In order for him to check the vulnerability of XYZ, he went through a few scanners that
are currently available. Here are the scanners that he uses:
1. Axent’s NetRecon (http://www.axent.com)
2. SARA, by Advanced Research Organization (http://www-arc.com/sara)
3. VLAD the Scanner, by Razor (http://razor.bindview.com/tools/)
However, there are many other alternative ways to make sure that the services that have been
scanned will be more accurate and detailed for Bob.
What would be the best method to accurately identify the services running on a victim host?
What will the SQL statement accomplish?
Jeremy is web security consultant for Information Securitas. Jeremy has just been hired to perform
contract work for a large state agency in Michigan. Jeremy’s first task is to scan all the company’s
external websites. Jeremy comes upon a login page which appears to allow employees access to
sensitive areas on the website. James types in the following statement in the username field:
SELECT * from Users where username=’admin’ ?AND password=” AND email like
‘%@testers.com%’
What will the SQL statement accomplish?