This attack technique is used when a Web application is vulnerable to an SQL Injection but the results of the
This attack technique is used when a Web application is vulnerable to an SQL Injection but the
results of the Injection are not visible to the attacker.
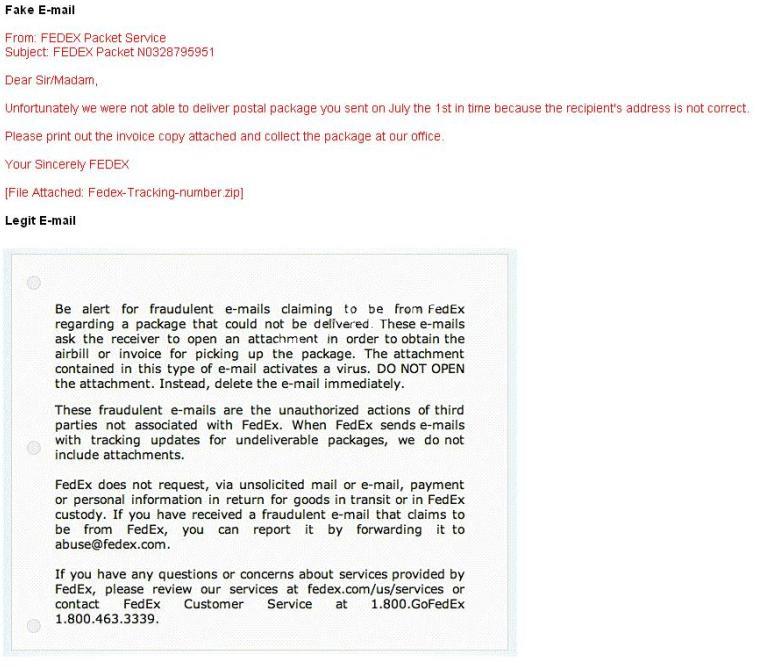
How do you ensure if the e-mail is authentic and sent from fedex.com?
A common technique for luring e-mail users into opening virus-launching attachments is to send
messages that would appear to be relevant or important to many of their potential recipients. One
way of accomplishing this feat is to make the virus-carrying messages appear to come from some
type of business entity retailing sites, UPS, FEDEX, CITIBANK or a major provider of a common
service.
Here is a fraudulent e-mail claiming to be from FedEx regarding a package that could not be
delivered. This mail asks the receiver to open an attachment in order to obtain the FEDEX tracking
number for picking up the package. The attachment contained in this type of e-mail activates a
virus.
Vendors send e-mails like this to their customers advising them not to open any files attached with
the mail, as they do not include attachments.
Fraudulent e-mail and legit e-mail that arrives in your inbox contain the fedex.com as the sender of
the mail.
How do you ensure if the e-mail is authentic and sent from fedex.com?
What file system vulnerability does the following command take advantage of?
What file system vulnerability does the following command take advantage of?
type c:\anyfile.exe > c:\winnt\system32\calc.exe:anyfile.exe
How would you resolve this situation?
You are the Security Administrator of Xtrinity, Inc. You write security policies and conduct
assessments to protect the company’s network. During one of your periodic checks to see how
well policy is being observed by the employees, you discover an employee has attached cell
phone 3G modem to his telephone line and workstation. He has used this cell phone 3G modem
to dial in to his workstation, thereby bypassing your firewall. A security breach has occurred as a
direct result of this activity. The employee explains that he used the modem because he had to
download software for a department project. How would you resolve this situation?
what stage of Virus life does a stealth virus gets activated with the user performing certain actions such as
In what stage of Virus life does a stealth virus gets activated with the user performing certain
actions such as running an infected program?
What is a sniffing performed on a switched network called?
What is a sniffing performed on a switched network called?
What privilege level does a rootkit require to infect successfully on a Victim’s machine?
A rootkit is a collection of tools (programs) that enable administrator-level access to a computer.
This program hides itself deep into an operating system for malicious activity and is extremely
difficult to detect. The malicious software operates in a stealth fashion by hiding its files,
processes and registry keys and may be used to create a hidden directory or folder designed to
keep out of view from a user’s operating system and security software.
What privilege level does a rootkit require to infect successfully on a Victim’s machine?
Which Steganography technique uses Whitespace to hide secret messages?
Which Steganography technique uses Whitespace to hide secret messages?
How would you detect IP spoofing?
Cyber Criminals have long employed the tactic of masking their true identity. In IP spoofing, an
attacker gains unauthorized access to a computer or a network by making it appear that a
malicious message has come from a trusted machine, by “spoofing” the IP address of that
machine.
How would you detect IP spoofing?
How can David block POP3 at the firewall?
David is a security administrator working in Boston. David has been asked by the office’s manager
to block all POP3 traffic at the firewall because he believes employees are spending too much
time reading personal email. How can David block POP3 at the firewall?