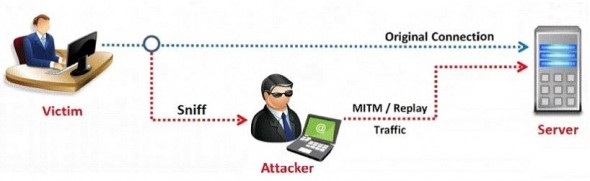
In this type of Man-in-the-Middle attack, packets and authentication tokens are captured using a sniffer. Once the relevant information is extracted, the tokens are placed back on the network to gain access.

A.
Token Injection Replay attacks
B.
Shoulder surfing attack
C.
Rainbow and Hash generation attack
D.
Dumpster diving attack