which of the following?
One of the system administrators at a company is assigned to maintain a secure computer lab. The
administrator has rights to configure machines, install software, and perform user account maintenance.
However, the administrator cannot add new computers to the domain, because that requires
authorization from the Information Assurance Officer. This is an example of which of the following?
Which of the following would be used to mitigate this issue so that only security administrators can make chan
A security administrator notices that a specific network administrator is making unauthorized changes to
the firewall every Saturday morning. Which of the following would be used to mitigate this issue so that
only security administrators can make changes to the firewall?
Which of the following risk mitigation strategies will allow Ann, a security analyst, to enforce least privile
Which of the following risk mitigation strategies will allow Ann, a security analyst, to enforce least
privilege principles?
Which of the following calculations would he security manager choose to determine total risk?
An IT security manager is asked to provide the total risk to the business. Which of the following
calculations would he security manager choose to determine total risk?
Which of the following, if implemented, would BEST reassure the CSO?
A company is preparing to decommission an offline, non-networked root certificate server. Before
sending the server’s drives to be destroyed by a contracted company, the Chief Security Officer (CSO)
wants to be certain that the data will not be accessed. Which of the following, if implemented, would
BEST reassure the CSO? (Select TWO).
which of the following concepts?
Identifying residual risk is MOST important to which of the following concepts?
which of the following core security areas?
A software company has completed a security assessment. The assessment states that the company
should implement fencing and lighting around the property. Additionally, the assessment states that
production releases of their software should be digitally signed. Given the recommendations, the
company was deficient in which of the following core security areas? (Select TWO).
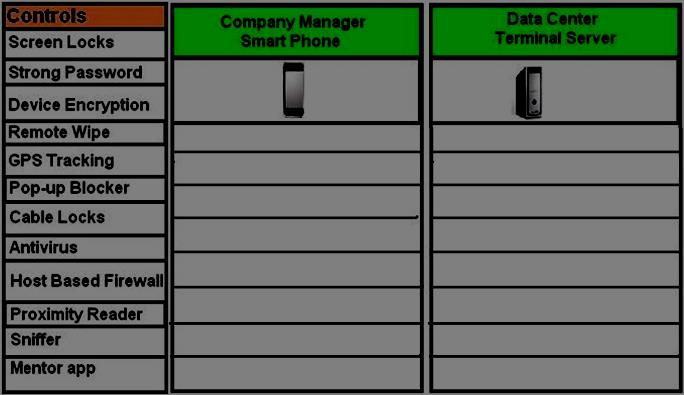
Drag and Drop the applicable controls to each asset type.
DRAG DROP
A Security administrator wants to implement strong security on the company smart phones and terminal
servers located in the data center. Drag and Drop the applicable controls to each asset type.Instructions: Controls can be used multiple times and not all placeholders needs to be filled. When you
have completed the simulation, Please select Done to submit.
Which of the following defines a business goal for system restoration and acceptable data loss?
Which of the following defines a business goal for system restoration and acceptable data loss?
Which of the following should Sara do to address the risk?
Sara, the Chief Security Officer (CSO), has had four security breaches during the past two years.
Each breach has cost the company $3,000. A third party vendor has offered to repair the security hole in
the system for $25,000. The breached system is scheduled to be replaced in five years.
Which of the following should Sara do to address the risk?