Which of the following controls could they implement to…
A company’s employees were victims of a spear phishing campaign impersonating the CEO. The company would now like to implement a solution to improve the
overall security posture by assuring their employees that email originated from the CEO. Which of the following controls could they implement to BEST meet this
goal?
Which of the following attack types is this?
Purchasing receives an automated phone call from a bank asking to input and verify credit card information. The phone number displayed on the caller ID matches
the bank. Which of the following attack types is this?
Which of the following attacks is being described?
Jane, an individual, has recently been calling various financial offices pretending to be another person to gain financial information. Which of the following attacks is
being described?
which of the following attacks?
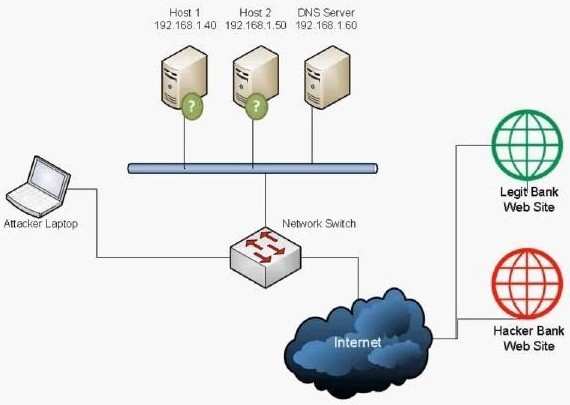
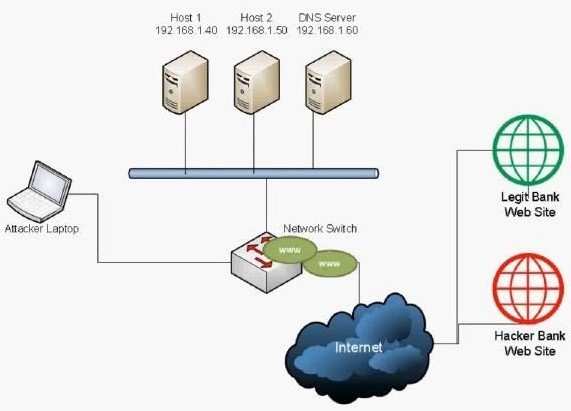
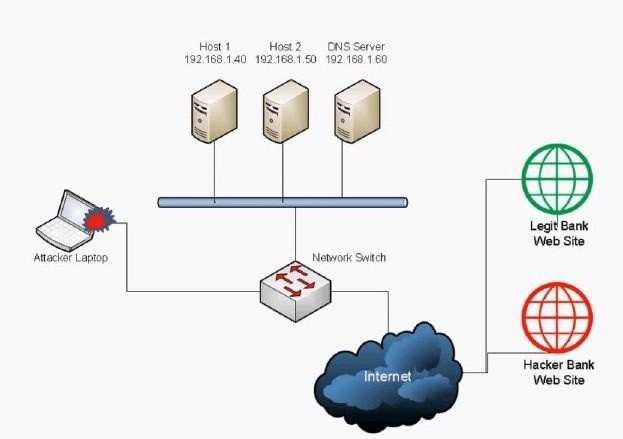
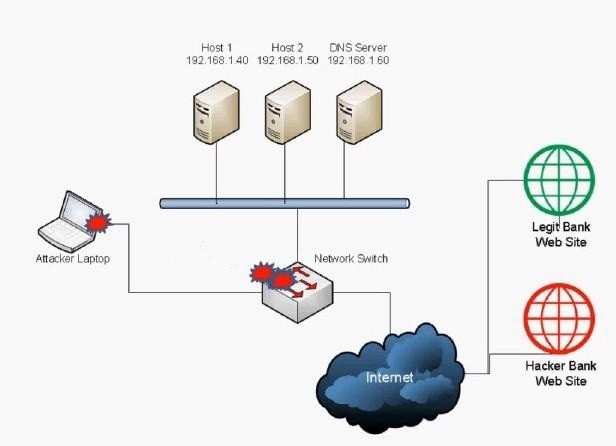
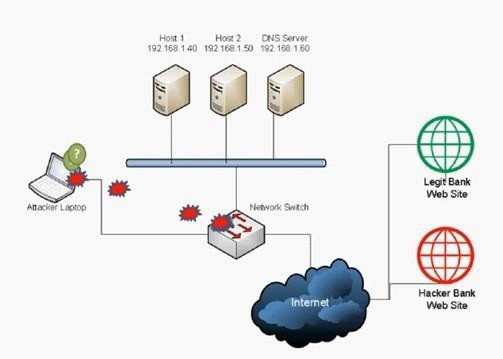
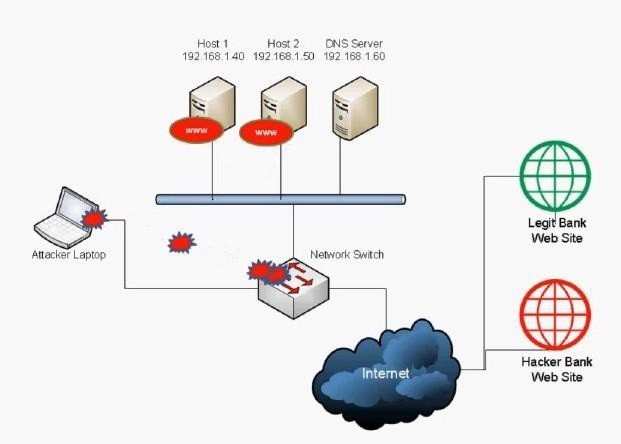
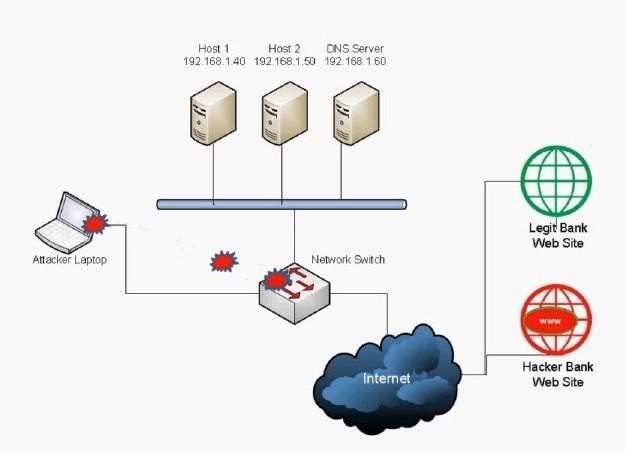
A security administrator notices large amounts of traffic within the network heading out to an external website. The website seems to be a fake bank site with a
phone number that when called, asks for sensitive information. After further investigation, the security administrator notices that a fake link was sent to several
users. This is an example of which of the following attacks?
which of the following?
Several users’ computers are no longer responding normally and sending out spam email to the users’ entire contact list. This is an example of which of the
following?
Which of the following is this an example of?
Mike, a user, states that he is receiving several unwanted emails about home loans. Which of the following is this an example of?
Which of the following BEST describes the type of attac…
Which of the following wireless security measures can a…
Which of the following wireless security measures can an attacker defeat by spoofing certain properties of their network interface card?
Which of the following will help prevent smurf attacks?
Which of the following will help prevent smurf attacks?