which of the following should the security technician respond?
A security technician is working with the network firewall team to implement access controls at the
company’s demarc as part of the initiation of configuration management processes. One of the network
technicians asks the security technician to explain the access control type found in a firewall. With which
of the following should the security technician respond?
which of the following information is MOST likely required?
During the information gathering stage of a deploying role-based access control model, which of the
following information is MOST likely required?
Which of the following configurations will meet the requirements?
A company hired Joe, an accountant. The IT administrator will need to create a new account for
Joe. The company uses groups for ease of management and administration of user accounts.
Joe will need network access to all directories, folders and files within the accounting department.
Which of the following configurations will meet the requirements?
Which of the following would be the MOST appropriate strategy for securing the server?
Users require access to a certain server depending on their job function. Which of the following would be
the MOST appropriate strategy for securing the server?
Which of the following controls is preventing them from completing their work?
The company’s sales team plans to work late to provide the Chief Executive Officer (CEO) with a special
report of sales before the quarter ends. After working for several hours, the team finds they cannot save
or print the reports.
Which of the following controls is preventing them from completing their work?
Which of the following security concepts can prevent a user from logging on from home during the weekends?
Which of the following security concepts can prevent a user from logging on from home during the
weekends?
Which of the following should the technician implement to meet managements request?
A technician is reviewing the logical access control method an organization uses. One of the senior
managers requests that the technician prevent staff members from logging on during nonworking days.
Which of the following should the technician implement to meet managements request?
Which of the following should be implemented in order to compliment password usage and smart cards?
Ann, the security administrator, wishes to implement multifactor security. Which of the following should
be implemented in order to compliment password usage and smart cards?
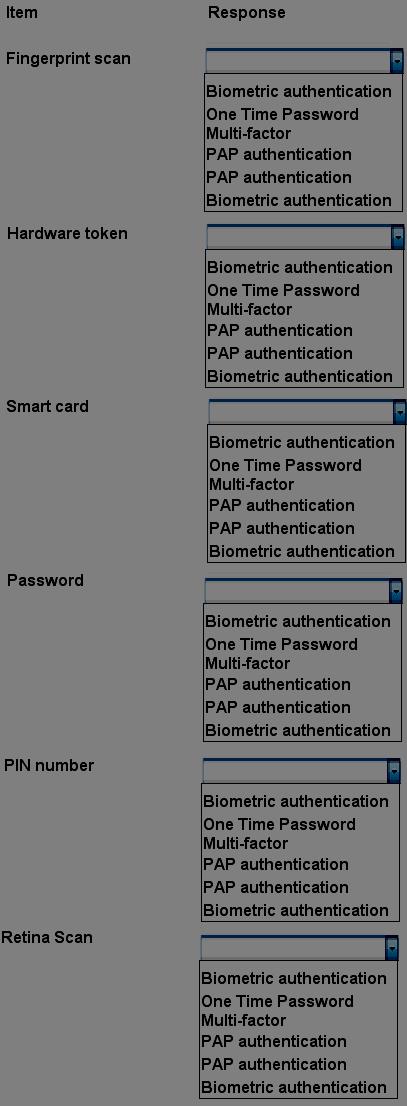
Select the appropriate authentication type for the following items:
which of the following?
A network administrator uses an RFID card to enter the datacenter, a key to open the server rack, and a
username and password to logon to a server. These are examples of which of the following?