Which of the following will the audit team most l likel…
During a third-party audit, it is determined that a member of the firewall team can request, approve, and
implement a new rule-set on the firewall. Which of the following will the audit team most l likely recommend
during the audit out brief?
Which of the following types of authorization could be …
Ann has read and written access to an employee database, while Joe has only read access. Ann is leaving for
a conference. Which of the following types of authorization could be utilized to trigger write access for Joe when
Ann is absent?
Which of the following is preventing the remote user fr…
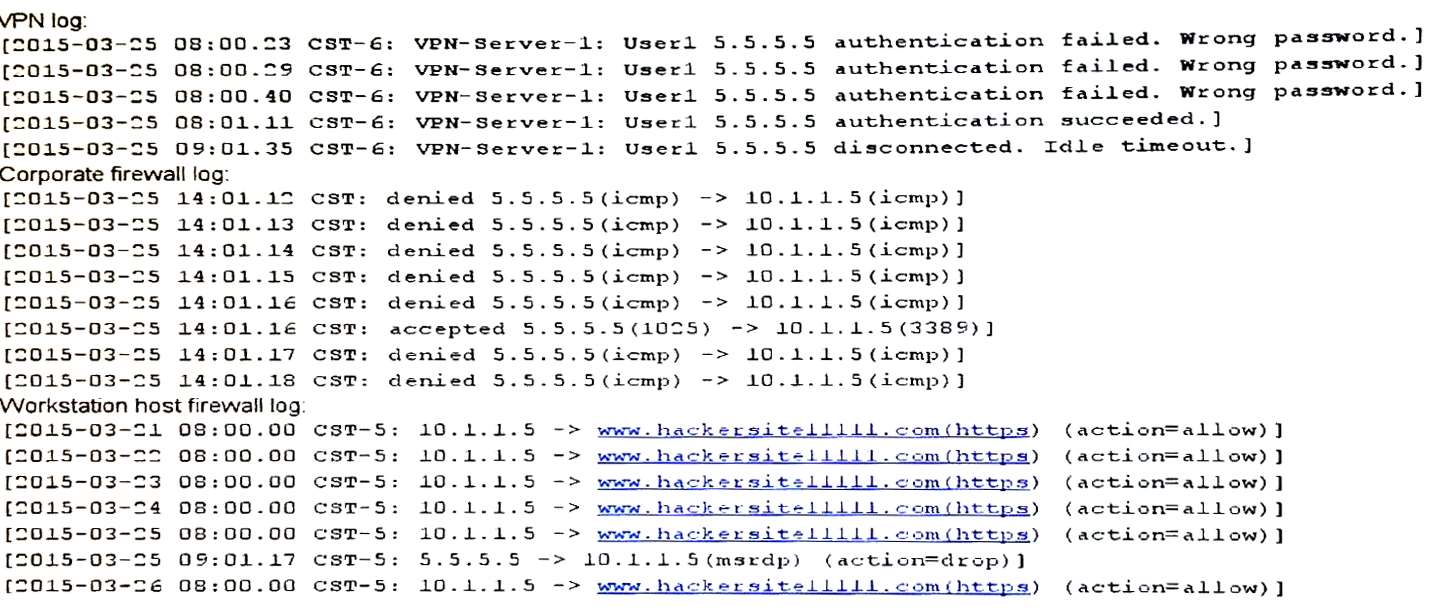
A remote user (User1) is unable to reach a newly provisioned corporate windows workstation. The system
administrator has been given the following log files from the VPN, corporate firewall and workstation host.
Which of the following is preventing the remote user from being able to access the workstation?
Which of the following would enhance the security of ac…
Which of the following would enhance the security of accessing data stored in the cloud? (Choose two.)
Which of the following controls should be implemented t…
The help desk is receiving numerous password change alerts from users in the accounting department. These
alerts occur multiple times on the same day for each of the affected users’ accounts. Which of the following
controls should be implemented to curtail this activity?
Which of the following delineates why it is important t…
Which of the following delineates why it is important to perform egress filtering and monitoring on Internet
connected security zones of interfaces on a firewall?
When designing a web based client server application wi…
When designing a web based client server application with single application server and database cluster
backend, input validation should be performed:
Which of the following techniques can be bypass a user …
Which of the following techniques can be bypass a user or computer’s web browser privacy settings? (Select
Two)
Which of the following is the MOST critical for immedia…
A datacenter manager has been asked to prioritize critical system recovery priorities. Which of the following is
the MOST critical for immediate recovery?
Which of the following methods should the security admi…
A security administrator needs an external vendor to correct an urgent issue with an organization’s physical
access control system (PACS). The PACS does not currently have internet access because it is running a
legacy operation system. Which of the following methods should the security administrator select the best
balances security and efficiency?