Which choice is the most feasible way for schools and parents to reduce cyber bullying?
The Internet has enabled many new anti-social activities, such as online stalking, cyber
bullying, and addiction to solitary online activities. Which choice is the most feasible way for
schools and parents to reduce cyber bullying?
Which solution would provide a more efficient way to categorize and share this information?
You are leading a team of new hires and need to train them on innovative strategies and
technologies that will be used to develop an upcoming project. You send several e-mail
messages with links to helpful resources. But you soon realize this is an inefficient way to
organize and share this information. Which solution would provide a more efficient way to
categorize and share this information?
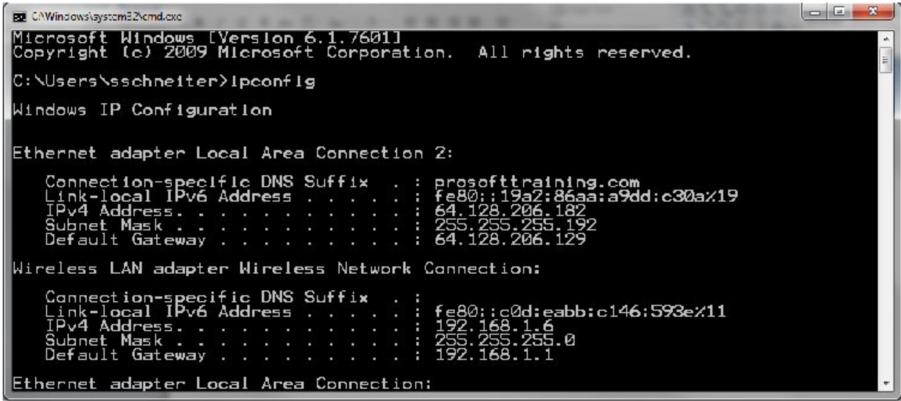
What does the Default Gateway identify?
what type of network?
You are distributing a large video game file using BitTorrent. First, you upload the initial file
and make it available via a central server called a tracker. Other users can then connect to
the tracker and download the file. Each user who downloads the file makes it available to
other users to download. The use of BitTorrent significantly reduces the original provider’s
hardware and bandwidth resource costs. BitTorrent is an example of what type of network?
Which of following is required to set up the e-mail account?
You are configuring an e-mail client to connect to your e-mail account. Which of following is
required to set up the e-mail account?
which an attacker attempts to steal personal or confidential information by sending e-mail that lures unsuspec
Which type of attack is a form of social engineering in which an attacker attempts to steal
personal or confidential information by sending e-mail that lures unsuspecting victims to log
in to an authentic-looking but imposter Web site?
What should Katie do to ensure that this site’s content renders consistently regardless of the browser used?
Katie developed her corporation’s intra net site using proprietary HTML language
extensions based on the company’s current browser. The company has recently updated its
systems to include the use of a new browser. Now the intra net site that Katie developed no
longer renders its content consistently. What should Katie do to ensure that this site’s
content renders consistently regardless of the browser used?
Which of the following is the most appropriate action for her to take?
Gabby suspects that an attacker has gained control of her system. Which of the following is
the most appropriate action for her to take?
Why should Marcella cancel her online transaction instead of proceeding?
Marcella is looking for a very unique product online. She has found one on the XYZ
Company’s Web site, which is designed well and appears to be legitimate. As she navigates
through the checkout process, she reaches the checkout page with this URL, which asks
her to enter her credit card information:
http://XYZ.com/gp/checkout.html/ref=chk_out_TLS12B_lb?ie=IJTFB&docld=10007931 Why
should Marcella cancel her online transaction instead of proceeding?
To accomplish this effectively in HTML5, Skylar should:
Skylar has been asked by the HR Department to create a Web page for the company’s intra
net site that compares the company’s four different medical insurance plans. To accomplish
this effectively in HTML5, Skylar should: