Which two actions should you perform?
A company has 10 client computers that run Windows 7. All client computers have the same
hardware configuration. The hardware configuration includes custom hardware components
manufactured by the company. The computer hard drives are configured as shown in the
Disk Management window exhibit. (Click the Exhibit button.)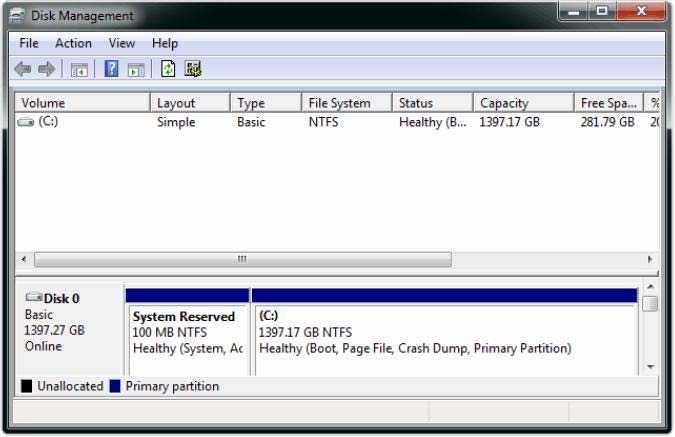
The company plans to upgrade the client computers to Windows 8.1.
You need to test hardware compatibility with Windows 8.1 on one client computer and leave
the existing Windows 7 installation intact.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
You need to configure unencrypted read access to file.txt for User2
You administer Windows 8.1 Pro computers in your company network.
A user named User1 encrypts a sensitive file named file.txt by using Encrypting File System
(EFS).
A user named User2 must be able to read file.txt.
You need to configure unencrypted read access to file.txt for User2.
What should you do?
you need to be able to recover a copy of any files from the library that have been changed within the last mon
You use a Windows 8.1 laptop.
You want to back up the Pictures library.
You need to configure a backup strategy that backs up the Pictures library to a network drive
every day. Additionally, you need to be able to recover a copy of any files from the library
that have been changed within the last month.
What should you do?
Which two actions should you perform on the client computers?
A company has client Windows Vista and Windows 8.1.
You need to ensure that the client computers can share local resources.
Which two actions should you perform on the client computers? (Each correct answer
presents part of the solution. Choose two.)
Which command should you use?
You administer Windows 8.1 client computers in your company network. The company has
an Active Directory Domain Services (AD DS) domain named contoso.com. The domain
contains a domain controller configured to lease DHCP and DHCPv6 addresses.
A client computer named Computer1 is configured to obtain IPv4 and IPv6 addresses
automatically.
A user reports that an IPv6-enabled application named Appl is not working on Computer1.
You discover that Computer1 has an IPv6 address prefix of FE80::. You are able to ping
Computer1 successfully by using IPv4, but when you use IPv6, your ping requests time out.
You need to ensure that Computer1 will support Appl.
Which command should you use?
You need to save the Windows Firewall with Advanced Security configuration settings from the reference compute
You administer Windows 8.1 Enterprise client computers in your company network.
You change settings on a reference computer by using the Windows Firewall with Advanced
Security tool. You want to apply the same settings to other computers.
You need to save the Windows Firewall with Advanced Security configuration settings from
the reference computer. You also need to be able to import the configuration settings into a
Group Policy object later.
What should you do?
You need to ensure that the network adapter settings of the client computer support joining a homegroup
A company has an Active Directory Domain Services (AD DS) domain. All client computers
run Windows 8.1 and are joined to the domain.
An employee is unable to connect his portable client computer to his home office
homegroup.
You need to ensure that the network adapter settings of the client computer support joining a
homegroup.
What should you do?
Which approach should you use to restore the folder?
You administer a Windows 8.1 Pro computer. The computer has File History turned on, and
system protection turned on for drive C.
You accidentally delete a folder named Libraries\Customers by using the Shift+Delete
keyboard shortcut.
You need to restore the most recent version of the folder to its original location.
Which approach should you use to restore the folder?
Which installation method should you use?
You use a computer that has Windows 7 Professional (32-bit) installed.
You need to migrate the computer to Windows 8.1 Pro (64-bit).
Which installation method should you use?
Which audit policy setting should you configure?
A company has Windows 8.1 client computers. All user data is stored locally. Each data file
has a system access control list (SACL).
You need to ensure that an event is generated when a user modifies a local file.
Which audit policy setting should you configure?

