What are two TCP flag settings that are considered suspicious?
What are two TCP flag settings that are considered suspicious? (Choose two.)
Which form of Web filtering is being used?
The Junos OS blocks an HTTP request due to a Websense server response. Which form of Web
filtering is being used?
Which two statements are true regarding redundancy groups?
Which two statements are true regarding redundancy groups? (Choose two.)
What are two components of the Junos software architecture?
What are two components of the Junos software architecture? (Choose two.)
Which IDP policy action closes the connection and sends an RST packet to both the client and the server?
Which IDP policy action closes the connection and sends an RST packet to both the client and the
server?
Which statement describes the UTM licensing model?
Which statement describes the UTM licensing model?
Which configuration would protect an SMTP server in the dmz zone from spam originating in the untrust zone?
You have configured a UTM profile called Block-Spam, which has the appropriate antispam
configuration to block undesired spam e-mails. Which configuration would protect an SMTP server
in the dmz zone from spam originating in the untrust zone?
Which two statements about the use of SCREEN options are correct?
Which two statements about the use of SCREEN options are correct? (Choose two.)
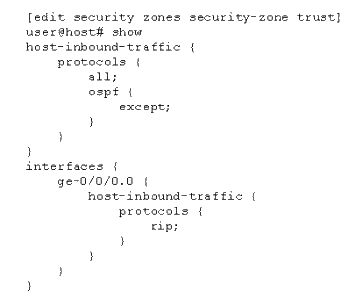
which protocol(s) are allowed to communicate with the device on ge-0/0/0.0?
Which two statements about static NAT are true?
Which two statements about static NAT are true? (Choose two.)