what is the cause of the problem?
Click the Exhibit button.
user@host> monitor traffic interface ge-0/0/3
verbose output suppressed, use <detail> or <extensive> for full protocol decode
Address resolution is ON. Use <no-resolve> to avoid any reverse lookup delay.
Address resolution timeout is 4s.
Listening on ge-0/0/3, capture size 96 bytes
Reverse lookup for 172.168.3.254 failed (check DNS reachability). Other reverse lookup failures will not be
reported.
Use <no-resolve> to avoid reverse lockups on IP addresses.
19:24:16.320907 In arp who-has 172.168.3.254 tell 172.168.3.1
19.24:17.322751 In arp who has 172.168.3.254 tell 172.168.3.1
19.24:18.328895 In arp who-has 172.168.3.254 tell 172.168.3.1
19.24:18.332956 In arn who has 172.168.3.254 tell 172.168.3.1
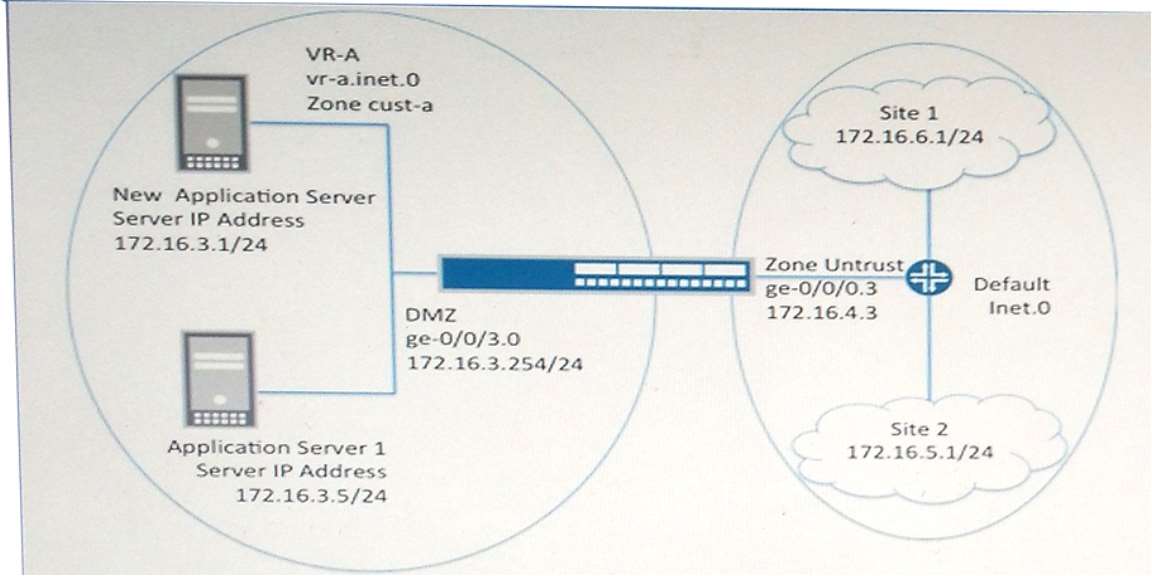
A new server has been set up in your environment. The administrator suspects that the firewall is blocking the
traffic from the new server. Previously existing servers in the VLAN are working correctly. After reviewing the
logs, you do not see any traffic for the new server.
Referring to the exhibit, what is the cause of the problem?
What must you do to correct the problem?
Click the Exhibit button.
user@host> show services application-identification application-system—cache
Application System Cache Configurations:
Application-cache: off
nested-application-cache: on
cache-unknown-result: on
cache-entry-timeout: 3600 seconds
You are using the application identification feature on your SRX Series device. The help desk reports that users
are complaining about slow Internet connectivity. You issue the command shown in the exhibit.
What must you do to correct the problem?
Which two statements are true about an interconnect log…
Which two statements are true about an interconnect logical system on an SRX Series device? (Choose two.)
Which two statements are true regarding the output show…
Click the Exhibit button.
[edit] user@host# run show log debug
Feb 3 22:04:31 22:04:31.824294:CID-0:RT:flow_first_policy_search: policy search from zone host-> zone
attacker (Ox0,0xe4089404,0x17)
Feb 3 22:04:31 22:04:31.824297:CID-0:RT:Policy lkup: vsys 0 zone(9:host) -> zone(10:attacker) scope: 0
Feb 3 22:04:31 22:04:31.824770:CID-0:RT: 5.0.0.25/59028 -> 25.0.0.25/23 proto 6
Feb 3 22:04:31 22:04:31.824778:CID-0:RT:Policy lkup: vsys 0 zone(5:Umkmowm) -> zone(5:Umkmowm)
scope: 0
Feb 3 22:04:31 22:04:31.824780:CID-0:RT: 5.0.0.25/59028 -> 25.0.0.25/23 proto 6
Feb 3 22:04:31 22:04:31.824783:CID-0:RT: app 10, timeout 1800s, curr ageout 20s
Feb 3 22:04:31 22:04:31.824785:CID-0:RT: permitted by policy default-policy-00(2)
Feb 3 22:04:31 22:04:31.824787:CID-0:RT: packet passed, Permitted by
policy.
Feb 3 22:04:31 22:04:31.824790:CID-0:RT:flow_first_src_xlate:
nat_src_xlated: False, nat_src_xlate_failed; False
Feb 3 22:04:31 22:04:31.824834:CID-0:RT:flow_first_src_xlate: incoming src port is: 38118
Which two statements are true regarding the output shown in the exhibit? (Choose two.)
what is causing this problem?
Click the Exhibit button.user@host# run show security flow session
…
Session ID: 28, Policy name: allow/5, Timeout: 2, Valid
In: 172.168.1.2/24800 –> 66.168.100.100/8001; tcp, If: ge-0/0/3.0, Pkts: 1, Bytes: 64
Out: 10.168.100.1/8001 –> 172.168.1.2/24800; tcp, If: ge-0/0/6.0, Pkts: 1, Bytes: 40
Your customer is unable to reach your HTTP server that is connected to the ge-0/0/6 interface. The HTTP
server has an address of 10.168.100.1 on port 80 internally, but is accessed publicly using interface ge-0/0/3
with the address 66.168.100.100 on port 8001.
Referring to the exhibit, what is causing this problem?
Which statement is correct?
You are asked to establish a hub-and-spoke IPsec VPN using your SRX Series device as the hub. All of your
spoke devices are third-party devices.
Which statement is correct?
which statement is correct?
Click the Exhibit button.
{primarynode0}[edit security idp idp-policy test-ips-policy]
user@host# show
rulebase-ips {
rule r1 {
match {
source-address any;
attacks {
predefined-attack-groups “HTTP – All”;
}
}
then {
action {
drop-packet;
}
}
terminal;
}
rule r2 {
match {
source-address 172.16.0.0/12;
attacks {
predefined-attack-groups “FTP – All”;
}
then {
action {
no-action;
}
}
}
rule r3 {
match {
source-address 172.16.0.0/12;
attacks {
predefined-attack-groups “TELNET – All”;
}
}
then {
action {
no-action;
}
}
}
rule r4 {match {
source-address any;
attacks {
predefined-attack-groups “FTP – All”;
}
}
then {
action {
drop-packet;
}
}
}
}
A user with IP address 172.301.100 initiates an FTP session to a host with IP address 10.100.1.50 through an
SRX Series device and is subject to the IPS policy shown in the exhibit.
cd ~root command, which statement is correct?
If the user tries to execute the
Which three tasks must be performed to make the feature…
You are asked to implement the AppFW feature on an SRX Series device.
Which three tasks must be performed to make the feature work? (Choose three.)
Which two statements must be considered when accomplish…
You are asked to implement a Dynamic IPsec VPN on your new SRX240. You are required to facilitate up to 5
simultaneous users.
Which two statements must be considered when accomplishing the task?
Which action resolves the problem?
You are using destination NAT to translate the address of your HTTPS server to a private address on your SRX
Series device. You have decided to implement IDP SSL decryption. Upon enabling the decryption, you notice
sessions are not decrypted.
Which action resolves the problem?