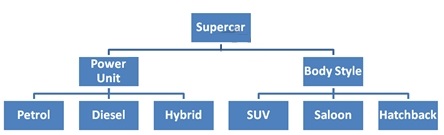
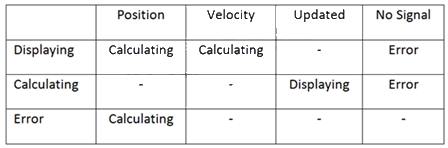
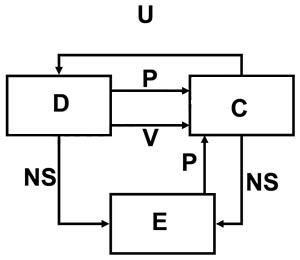
How many invalid test cases can be identified from the “Route Calculation” state table provided?
How many invalid test cases can be identified from the “Route Calculation” state table provided?
You may assume all actions are different and independent.
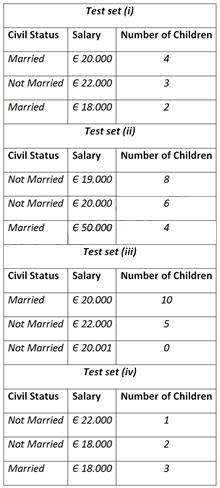
Which of the following test sets will provide the best equivalence partitioning coverage?
A diamond retailer is introducing a new stock taking system. Each diamond is assigned a
character that represents the colour. The valid domain for the character ranges from D to Z. The
colour is then graded using the following scale: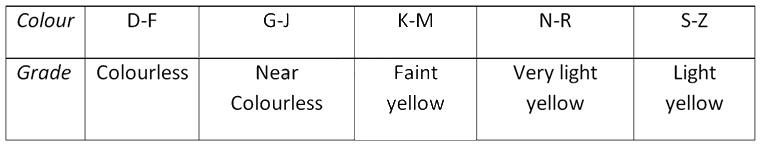
Which of the following test sets will provide the best equivalence partitioning coverage?
which other specification-based technique would you additionally choose to test the interfaces between compone
Apart from state transition testing, which other specification-based technique would you
additionally choose to test the interfaces between components of “Route Calculation” and thus
typically find different types of defects?
Identify the MOST likely technique from the following list.
Which of the following test design techniques is LEAST likely to be used for identifying test cases for the re
Analyzing the requirement, “The system shall allow cash advances of at least 200 Euros for all
supported credit cards. The correct list of credit cards is American Express, Diners, VISA,
Mastercard and Eurocard.” There are arguments to be made for several test design techniques.
Which of the following test design techniques is LEAST likely to be used for identifying test cases
for the requirement?
Which of the following test design techniques is specifically targeted at such failures?
For an ATM banking project introduced earlier, “When the user first inserts a valid credit card type,
the system considers the user to be in an unauthenticated state. When requesting a cash
advance, the user must be in an authenticated state. The user authenticates by entering the
proper PIN code. When authenticating the user, the system shall allow the user to enter their PIN
code up to three times before failing the authentication and rejecting the card. On the first and
second try, the system shall prompt the user to re-enter the PIN code.”
Suppose you are concerned that, depending on the exact number of invalid PIN codes entered,
the system might behave improperly. Which of the following test design techniques is specifically
targeted at such failures?
which of the following statements is correct?
how many test cases are needed to achieve 1-switch coverage?
which would be the most interesting test set to explicitly test one single boundary value as defined in the �
Which of the following test techniques will you use to the processing functionality of the traffic control sys
You are testing the processing of a critical traffic control system to which various regulations apply.
The processing of the input variables is dependent of defined ranges within which the actual
retrieved data values can lie.
Which of the following test techniques will you use to the processing functionality of the traffic
control system?
Which of the following descriptions is an example of the use of defect taxonomies?
Which of the following descriptions is an example of the use of defect taxonomies?
Number of correct answers: 1