Which of the following is the BEST method to assess the effectiveness of an organization’s vulnerability
Which of the following is the BEST method to assess the effectiveness of an organization’s
vulnerability management program?
Which methodology is recommended for penetration testing to be effective in the development phase of the life-
Which methodology is recommended for penetration testing to be effective in the development
phase of the life-cycle process?
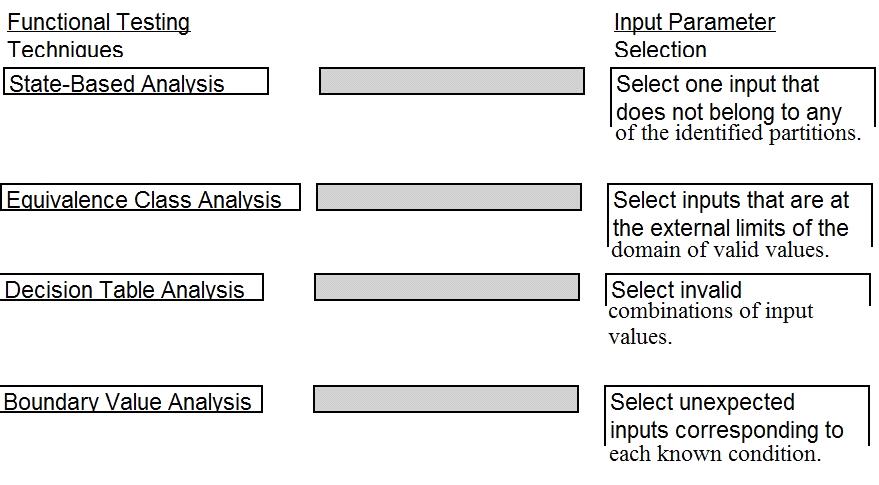
Match the functional testing techniques on the left with the correct input parameters on the right.
Which of the following is most helpful in applying the principle of LEAST privilege?
Which of the following is most helpful in applying the principle of LEAST privilege?
Which of the following explains why record destruction requirements are included in a data retention policy?
Which of the following explains why record destruction requirements are included in a data
retention policy?
What should happen when an emergency change to a system must be performed?
What should happen when an emergency change to a system must be performed?
Which of the following is the BEST approach to take in order to effectively incorporate the concepts of busine
Which of the following is the BEST approach to take in order to effectively incorporate the concepts
of business continuity into the organization?
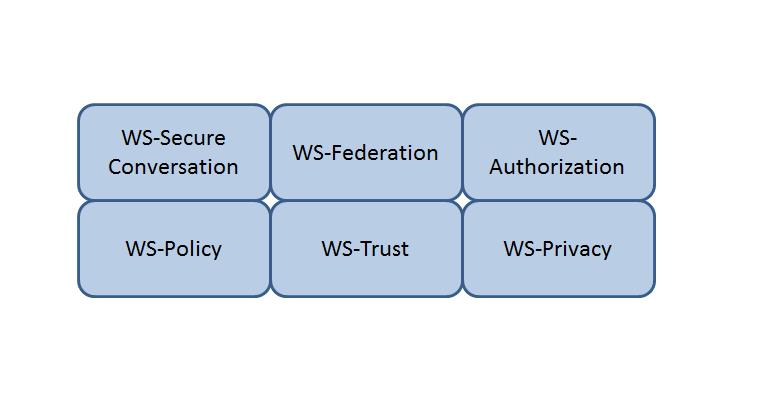
Which Web Services Security (WS-Security) specification maintains a single authenticated identity across multi
Which of the following has the GREATEST impact on an organization’s security posture?
Which of the following has the GREATEST impact on an organization’s security posture?
which of the following standards would BEST reduce the potential for data breaches?
The application of which of the following standards would BEST reduce the potential for data
breaches?