Which of the following MOST influences the design of the organization’s electronic monitoring policies?
Which of the following MOST influences the design of the organization’s electronic monitoring
policies?
which type of attack?
Without proper signal protection, embedded systems may be prone to which type of attack?
Which of the following is a detective access control mechanism?
Which of the following is a detective access control mechanism?
Which of the following BEST describes Recovery Time Objective (RTO)?
Which of the following BEST describes Recovery Time Objective (RTO)?
Which of the following is a PRIMARY security concern?
An organization publishes and periodically updates its employee policies in a file on their intranet.
Which of the following is a PRIMARY security concern?
Which of the following is a valid reason a customer transaction is kept beyond…?
An online retail company has formulated a record retention schedule for customer transactions.
Which of the following is a valid reason a customer transaction is kept beyond the retention
schedule?
Which of the following is the MAIN goal of a data retention policy?
Which of the following is the MAIN goal of a data retention policy?
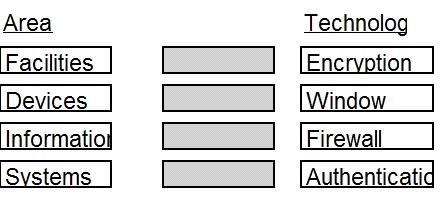
Given the various means to protect physical and logical assets, match the access management…
Which of the following problems is not addressed by using OAuth (Open Standard to Authorization) 2.0 to integr
Which of the following problems is not addressed by using OAuth (Open Standard to Authorization)
2.0 to integrate a third-party identity provider for a service?
what type of security control?
The use of proximity card to gain access to a building is an example of what type of security control?