Which Worklight pre-defined authentication methods can be used to secure an application that does not require
Which Worklight pre-defined authentication methods can be used to secure an application that
does not require the user to login interactively?
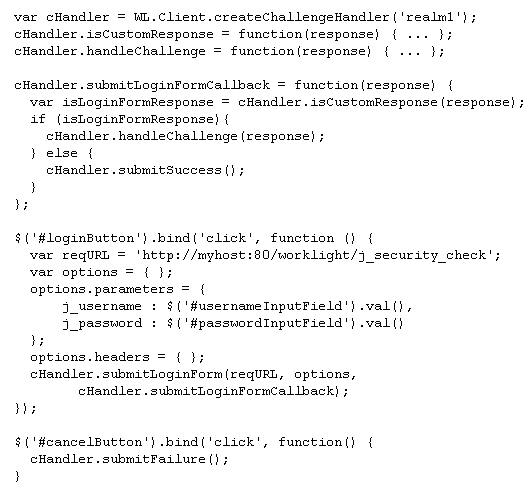
What is the problem with this challenge handler?
Which three components must be implemented when defining an authentication realm?
Which three components must be implemented when defining an authentication realm? (Choose
three.)
properties file to properly configure it for deployment to the production environment?
A developer is preparing a Worklight mobile application for deployment to a production
environment where the Worklight Server core database is stored on DB2 and must be accessed
using the WorklightDS data source.
Which database properly settings must the developer specify in the application’s worklight.
properties file to properly configure it for deployment to the production environment?