which of the following is likely to be installed on the…
A penetration tester is conducting a port scan on a specific host. The tester found several ports opened that
were confusing in concluding the Operating System (OS) version installed. Considering the NMAP result below,
which of the following is likely to be installed on the target machine by the OS?
Starting NMAP 5.21 at 2011-03-15 11:06 NMAP scan report for 172.16.40.65 Host is up (1.00s latency). Not
shown: 993 closed ports PORT STATE SERVICE 21/tcp open ftp 23/tcp open telnet 80/tcp open http 139/tcp
open netbios-ssn 515/tcp open 631/tcp open ipp 9100/tcp open MAC Address: 00:00:48:0D:EE:8
What is one of the first things you should do when give…
You’ve just been hired to perform a pen test on an organization that has been subjected to a large-scale attack.
The CIO is concerned with mitigating threats and vulnerabilities to totally eliminate risk.
What is one of the first things you should do when given the job?
Which command-line utility are you most likely to use?
You have several plain-text firewall logs that you must review to evaluate network traffic. You know that in order
to do fast, efficient searches of the logs you must use regular expressions.
Which command-line utility are you most likely to use?
Which of the following describes the characteristics of…
Which of the following describes the characteristics of a Boot Sector Virus?
What should you do?
You are performing a penetration test. You achieved access via a buffer overflow exploit and you proceed to
find interesting data, such as files with usernames and passwords. You find a hidden folder that has the
administrator’s bank account password and login information for the administrator’s bitcoin account.
What should you do?
What item is the primary concern on OWASP’s Top Ten Pro…
The Open Web Application Security Project (OWASP) is the worldwide not-for-profit charitable organization
focused on improving the security of software. What item is the primary concern on OWASP’s Top Ten Project
Most Critical Web Application Security Risks?
What is the process of logging, recording, and resolvin…
What is the process of logging, recording, and resolving events that take place in an organization?
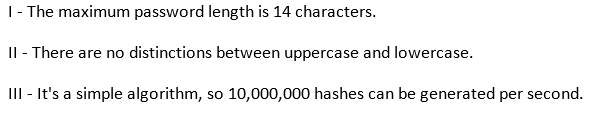
Which of the following parameters describe LM Hash (see…
What cipher is described above?
This asymmetry cipher is based on factoring the product of two large prime numbers.
What cipher is described above?
What wireshark filter will show the connections from th…
You are a Network Security Officer. You have two machines. The first machine (192.168.0.99) has snort
installed, and the second machine (192.168.0.150) has kiwi syslog installed. You perform a syn scan in your
network, and you notice that kiwi syslog is not receiving the alert message from snort. You decide to run
wireshark in the snort machine to check if the messages are going to the kiwi syslog machine.
What wireshark filter will show the connections from the snort machine to kiwi syslog machine?