Which of the following deposition is not a standard practice?
Deposition enables opposing counsel to preview an expert witness’s testimony at trial. Which of
the following deposition is not a standard practice?
how many sectors are normally allocated to this file?
If a file (readme.txt) on a hard disk has a size of 2600 bytes, how many sectors are normally
allocated to this file?
Recovery of the deleted partition is the process by which the investigator evaluates and extracts the deleted
Recovery of the deleted partition is the process by which the investigator evaluates and extracts
the deleted partitions.
During first responder procedure you should follow all laws while collecting the evidence, and contact a compu
During first responder procedure you should follow all laws while collecting the evidence, and
contact a computer forensic examiner as soon as possible
Which one of the following is not a consideration in a forensic readiness planning checklist?
Which one of the following is not a consideration in a forensic readiness planning checklist?
When collecting electronic evidence at the crime scene, the collection should proceed from the most volatile t
When collecting electronic evidence at the crime scene, the collection should proceed from the
most volatile to the least volatile
What is a chain of custody?
What is a chain of custody?
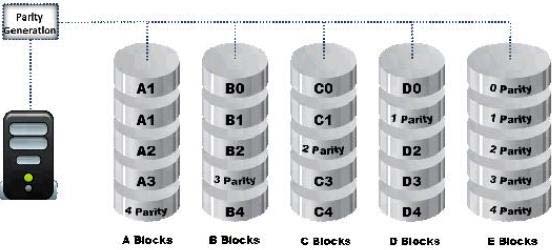
What RAID level is represented here?
Which of the following attributes of a forensics report can render it inadmissible in a court of law?
Computer forensics report provides detailed information on complete computer forensics
investigation process. It should explain how the incident occurred, provide technical details of the
incident and should be clear to understand. Which of the following attributes of a forensics report
can render it inadmissible in a court of law?
Email spoofing refers to:
Email spoofing refers to: