What is a sniffing performed on a switched network called?
What is a sniffing performed on a switched network called?
What does a type 3 code 13 represent?
What does a type 3 code 13 represent?(Choose two.
What privilege level does a rootkit require to infect successfully on a Victim’s machine?
A rootkit is a collection of tools (programs) that enable administrator-level access to a computer.
This program hides itself deep into an operating system for malicious activity and is extremely
difficult to detect. The malicious software operates in a stealth fashion by hiding its files,
processes and registry keys and may be used to create a hidden directory or folder designed to
keep out of view from a user’s operating system and security software.
What privilege level does a rootkit require to infect successfully on a Victim’s machine?
Destination unreachable administratively prohibited messages can inform the hacker to what?
Destination unreachable administratively prohibited messages can inform the hacker to what?
Which of the following Nmap commands would be used to perform a stack fingerprinting?
Which of the following Nmap commands would be used to perform a stack fingerprinting?
Which Steganography technique uses Whitespace to hide secret messages?
Which Steganography technique uses Whitespace to hide secret messages?
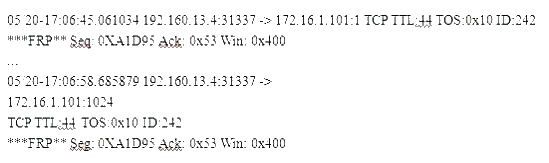
What is odd about this attack?
(Note: the student is being tested on concepts learnt during passive OS fingerprinting, basic
TCP/IP connection concepts and the ability to read packet signatures from a sniff dump.)
Snort has been used to capture packets on the network. On studying the packets, the penetration
tester finds it to be abnormal. If you were the penetration tester, why would you find this
abnormal?
What is odd about this attack? Choose the best answer.
How would you detect IP spoofing?
Cyber Criminals have long employed the tactic of masking their true identity. In IP spoofing, an
attacker gains unauthorized access to a computer or a network by making it appear that a
malicious message has come from a trusted machine, by “spoofing” the IP address of that
machine.
How would you detect IP spoofing?
Which type of Nmap scan is the most reliable, but also the most visible, and likely to be picked up by and IDS
Which type of Nmap scan is the most reliable, but also the most visible, and likely to be picked up
by and IDS?
How can David block POP3 at the firewall?
David is a security administrator working in Boston. David has been asked by the office’s manager
to block all POP3 traffic at the firewall because he believes employees are spending too much
time reading personal email. How can David block POP3 at the firewall?