Attackers send a legitimate-looking e-mail asking users to update their information on the company’s Web
This attack uses social engineering techniques to trick users into accessing a fake Web site and
divulging personal information. Attackers send a legitimate-looking e-mail asking users to update
their information on the company’s Web site, but the URLs in the e-mail actually point to a false
Web site.
What does this suggest?
An Nmap scan shows the following open ports, and nmap also reports that the OS guessing
results to match too many signatures hence it cannot reliably be identified:
21 ftp
23 telnet
80 http
443 https
What does this suggest?
Which of the following statements would NOT be a proper definition for a Trojan Horse?
Which of the following statements would NOT be a proper definition for a Trojan Horse?
What port scanning method involves sending spoofed packets to a target system and then looking for adjustments
What port scanning method involves sending spoofed packets to a target system and then looking
for adjustments to the IPID on a zombie system?
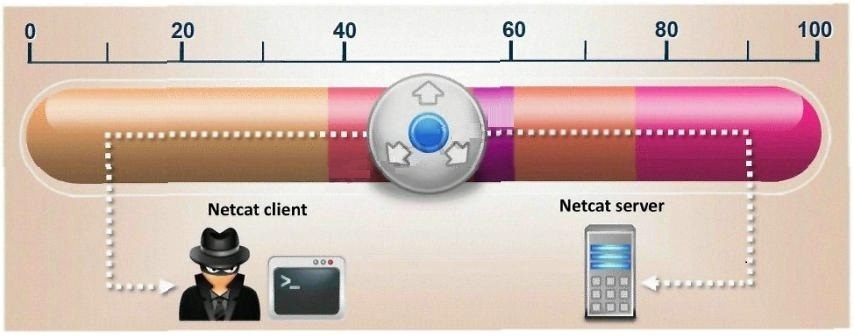
What is the correct command to run Netcat on a server using port 56 that spawns command shell when connected?
What port scanning method is the most reliable but also the most detectable?
What port scanning method is the most reliable but also the most detectable?
SNMP is a connectionless protocol that uses UDP instead of TCP packets (True or False)
SNMP is a connectionless protocol that uses UDP instead of TCP packets (True or False)
What does an ICMP (Code 13) message normally indicates?
What does an ICMP (Code 13) message normally indicates?
which OSI layer?
TCP/IP Session Hijacking is carried out in which OSI layer?
Because UDP is a connectionless protocol: (Select 2)
Because UDP is a connectionless protocol: (Select 2)