what would the following command accomplish?
Using Linux to carry out a forensics investigation, what would the following command accomplish?
dd if=/usr/home/partition.image of=/dev/sdb2 bs=4096 conv=notrunc,noerror
which US Amendment is Madison lawyer trying to prove the police violated?
Madison is on trial for allegedly breaking into her university internal network. The police raided her dorm room and seized all of her computer equipment. Madison lawyer is trying to convince the judge that the seizure was unfounded and baseless.
Under which US Amendment is Madison lawyer trying to prove the police violated?
When is it appropriate to use computer forensics?
When is it appropriate to use computer forensics?
Why is it still possible to recover files that have been emptied from the Recycle Bin on a Windows computer?
Why is it still possible to recover files that have been emptied from the Recycle Bin on a Windows computer?
where on the domain controllers are the passwords stored?
On an Active Directory network using NTLM authentication, where on the domain controllers are the passwords stored?
This type of testimony is presented by someone who does the actual fieldwork and does not offer a view in cour
This type of testimony is presented by someone who does the actual fieldwork and does not offer a view in court.
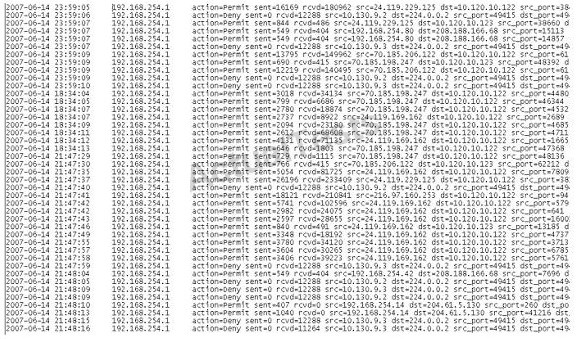
what information can be obtained from the DHCP logs?
When investigating a wireless attack, what information can be obtained from the DHCP logs?
One way to identify the presence of hidden partitions on a suspect hard drive is to:
One way to identify the presence of hidden partitions on a suspect hard drive is to: