What technique is used by JPEGs for compression?
What technique is used by JPEGs for compression?
which operating system to write hard drive data?
Lockdown device uses which operating system to write hard drive data?
Where could the investigator search to find the message tracking log file on the Exchange server?
During an investigation, an employee was found to have deleted harassing emails that were sent to someone else. The company was using Microsoft Exchange and had message tracking enabled.
Where could the investigator search to find the message tracking log file on the Exchange server?
What is the first step that Paul must take with the PDA to ensure the integrity of the investigation?
Paul is a computer forensics investigator working for Tyler & Company Consultants. Paul has been called upon to help investigate a computer hacking ring broken up by the local police. Paul begins to inventory the PCs found in the hackers hideout.
Paul then comes across a PDA left by them that is attached to a number of different peripheral devices.
What is the first step that Paul must take with the PDA to ensure the integrity of the investigation?
What must be obtained before an investigation is carried out at a location?
What must be obtained before an investigation is carried out at a location?
How many times can data be written to a DVD+R disk?
How many times can data be written to a DVD+R disk?
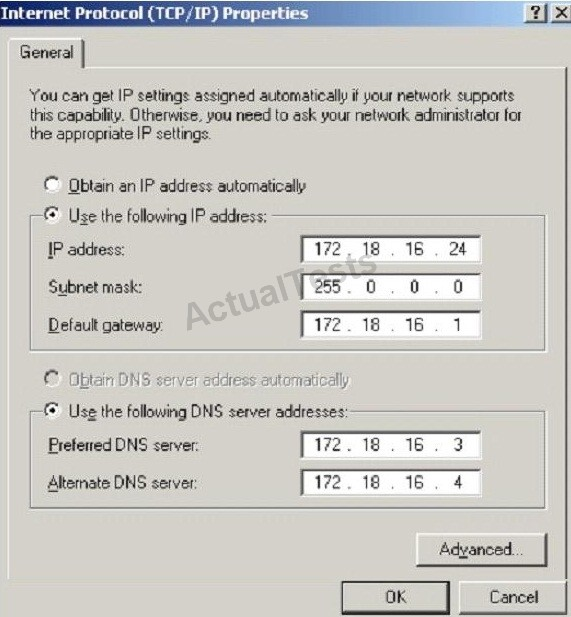
What is the CIDR from the following screenshot?
What type of steganography did these two suspects use?
Harold is a computer forensics investigator working for a consulting firm out of Atlanta Georgia. Harold is called upon to help with a corporate espionage case in Miami Florida. Harold assists in the investigation by pulling all the data from the computers allegedly used in the illegal activities. He finds that two suspects in the company where stealing sensitive corporate information and selling it to competing companies. From the email and instant messenger logs recovered, Harold has discovered that the two employees notified the buyers by writing symbols on the back of specific stop signs. This way, the buyers knew when and where to meet with the alleged suspects to buy the stolen material.
What type of steganography did these two suspects use?
What type of attack sends SYN requests to a target system with spoofed IP addresses?
What type of attack sends SYN requests to a target system with spoofed IP addresses?
What term is used to describe a cryptographic technique for embedding information into something else for the
What term is used to describe a cryptographic technique for embedding information into something else for the sole purpose of hiding that information from the casual observer?