Which of the following tools is John using to crack the wireless encryption keys?
John works as a professional Ethical Hacker. He has been assigned the project of testing the
security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys. The
description of the tool is as follows: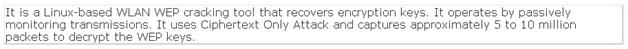
Which of the following tools is John using to crack the wireless encryption keys?
Which of the following is a process that detects a problem, determines its cause, minimizes the damages…
Which of the following is a process that detects a problem, determines its cause, minimizes the
damages, resolves the problem, and documents each step of response for future reference?
Which of the following is designed to detect the unwanted presence of fire by monitoring environmental changes
Which of the following is designed to detect the unwanted presence of fire by monitoring
environmental changes associated with combustion?
Which of the following is an intrusion detection system that monitors and analyzes the internals of a computin
Which of the following is an intrusion detection system that monitors and analyzes the internals of
a computing system rather than the network packets on its external interfaces?
Which of the following types of VPN uses the Internet as its main backbone, allowing users, customers, and bra
Which of the following types of VPN uses the Internet as its main backbone, allowing users,
customers, and branch offices to access corporate network resources across various network
architectures?
Which of the following is a protocol that describes an approach to providing "streamlined" support o
Which of the following is a protocol that describes an approach to providing “streamlined” support
of OSI application services on top of TCP/IP-based networks for some constrained environments?
Which of the following is the best way to address this issue?
You are an Administrator for a network at an investment bank. You are concerned about
individuals breeching your network and being able to steal data before you can detect their
presence and shut down their access. Which of the following is the best way to address this
issue?
Which of the following is the practice of sending unwanted e-mail messages, frequently with commercial content
Which of the following is the practice of sending unwanted e-mail messages, frequently with
commercial content, in large quantities to an indiscriminate set of recipients? Each correct answer
represents a complete solution. Choose all that apply.
The ____________risk analysis process analyzes the effect of a risk event deriving a numerical value
CORRECT TEXT
Fill in the blank with the appropriate word. The ____________________risk analysis process
analyzes the effect of a risk event deriving a numerical value.
Which of the following is a tool that runs on the Windows OS and analyzes iptables log messages to detect port
Which of the following is a tool that runs on the Windows OS and analyzes iptables log messages
to detect port scans and other suspicious traffic?

