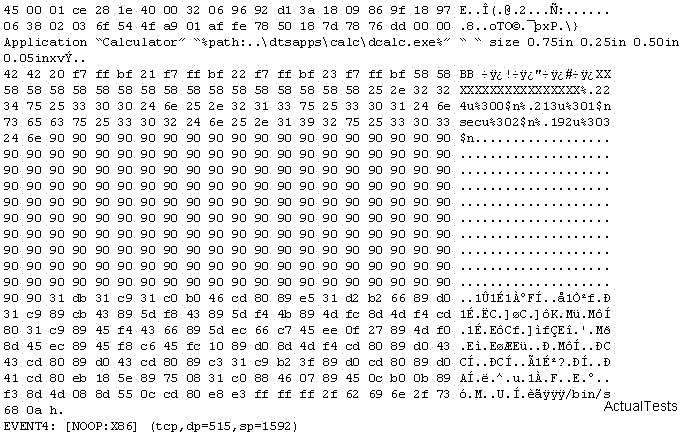
The following is an entry captured by a network IDS. You are assigned the task of analyzing this entry. You notice the value 0x90, which is the most common NOOP instruction for the Intel processor. You figure that the attacker is attempting a buffer overflow attack. You also notice “/bin/sh” in the ASCII part of the output. As an analyst what would you conclude about the attack?

A.
The attacker is attempting a buffer overflow attack and has succeeded
B.
The buffer overflow attack has been neutralized by the IDS
C.
The attacker is creating a directory on the compromised machine
D.
The attacker is attempting an exploit that launches a command-line shell
Explanation:
This log entry shows a hacker using a buffer overflow to fill the data buffer and trying to insert the execution of /bin/sh into the executable code part of the thread. It is probably an existing exploit that is used, or a directed attack with a custom built buffer overflow with the “payload” that launches the command shell.