A system administrator is reviewing the following information from a compromised server.
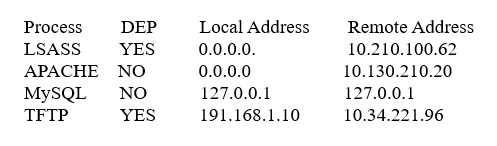
Given the above information, which of the following processes was MOST likely exploited via remote buffer overflow attack?
A. Apache
B. LSASS
C. MySQL
D. TFTP

