Which of the following technologies would be MOST appro…
Which of the following technologies would be MOST appropriate to utilize when testing a new software patch
before a company-wide deployment?
Which of the following would verify that a threat does …
Which of the following would verify that a threat does exist and security controls can easily be bypassed without
actively testing an application?
Which of the following would BEST help them establish p…
A security team wants to establish an Incident Response plan. The team has never experienced an incident.
Which of the following would BEST help them establish plans and procedures?
Which of the following attacks is being attempted?
An administrator discovers the following log entry on a server:
Nov 12 2013 00:23:45 httpd[2342]: GET /app2/prod/proc/process.php?input=change;cd
%20../../../etc;cat%20shadow
Which of the following attacks is being attempted?
Which of the following types of attacks is this MOST likely?
Anne, the Chief Executive Officer (CEO), has reported that she is getting multiple telephone calls from
someone claiming to be from the helpdesk. The caller is asking to verify her network authentication credentials
because her computer is broadcasting across the network.
Which of the following types of attacks is this MOST likely?
Which of the following principles BEST describes the we…
Phishing emails frequently take advantage of high-profile catastrophes reported in the news.
Which of the following principles BEST describes the weakness being exploited?
Which of the following is the reason the manager instal…
A network operations manager has added a second row of server racks in the datacenter. These racks face the
opposite direction of the first row of racks.
Which of the following is the reason the manager installed the racks this way?
You need to eliminate the redundancy while maintaining …
SIMULATION
You have just received some room and Wi-Fi access control recommendations from a security consulting
company. Click on each building to bring up available security controls. Please implement the following
requirements:
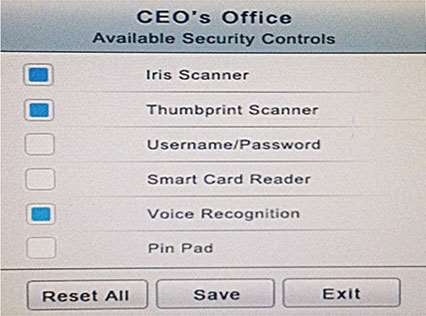
The Chief Executive Officer’s (CEO) office had multiple redundant security measures installed on the door
to the office. Remove unnecessary redundancies to deploy three-factor authentication, while retaining the
expensive iris render.
The Public Cafe has wireless available to customers. You need to secure the WAP with WPA and place a
passphrase on the customer receipts.
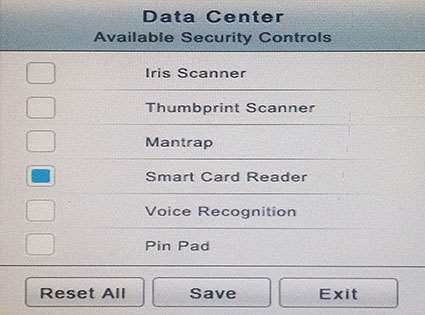
In the Data Center you need to include authentication from the “something you know” category and take
advantage of the existing smartcard reader on the door.
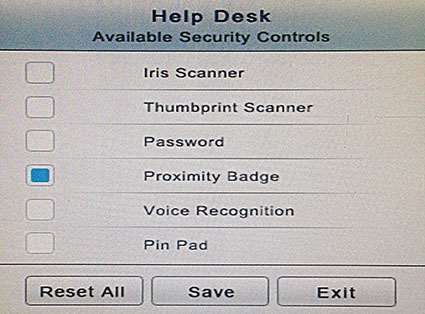
In the Help Desk Office you need to require single factor authentication through the use of physical tokens
given to guests by the receptionist.
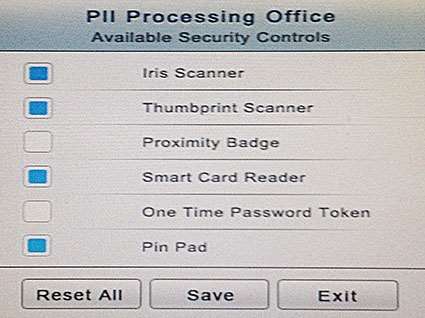
The PII Office has redundant security measures in place. You need to eliminate the redundancy while
maintaining three-factor authentication and retaining the more expensive controls.
Company XYZ Corporate headquarters Building
Instructions: The original security controls for each office can be reset at anytime by selecting the Reset
button. Once you have met the above requirements for each office, select the Save button. When you have
completed the entire simulation, please select the Done button to submit. Once the simulation is submitted,
please select the Next button to continue.
Simulation
Which of the following should be configured on the VPN …
A system administrator is configuring a site-to-site VPN tunnel. Which of the following should be configured on
the VPN concentrator during the IKE phase?
This message is an example of:
Joe, the security administrator, sees this in a vulnerability scan report:
“The server 10.1.2.232 is running Apache 2.2.20 which may be vulnerable to a
mod_cgi exploit.”
Joe verifies that the mod_cgi module is not enabled on 10.1.2.232. This message is an example of: