Which of the following applications can help determine whether a denial-of-service attack is occurring against
Which of the following applications can help determine whether a denial-of-service attack is
occurring against a network host?
Which of the following is a primary concern for this solution?
You have just deployed an application that uses hash-based checksums to monitor changes in the
configuration scripts of a database server that is accessible via the Internet. Which of the following
is a primary concern for this solution?
Which of the following activities is the most effective at keeping the actions of na?e end users from putting
Which of the following activities is the most effective at keeping the actions of nae end users from
putting the company’s physical and logicalWhich of the following activities is the most effective at
keeping the actions of na?e end users from putting the company’s physical and logical resources
at risk?
which of the following resources should you audit the most aggressively?
Your organization has made a particularly unpopular policy decision. Your supervisor fears that a
series of attacks may occur as a result. You have been assigned to increase automated auditing
on a server. When fulfilling this request, which of the following resources should you audit the
most aggressively?
Which type of attack is this?
Jason is attempting to gain unauthorized access to a corporate server by running a program that
enters passwords from a long list of possible passwords. Which type of attack is this?
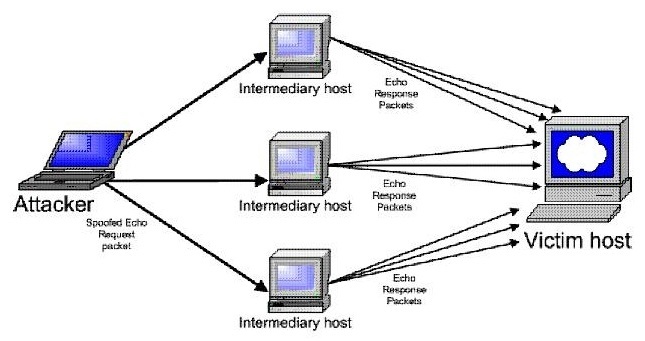
Which type of attack is occurring?
Which of the following is a primary weakness of asymmetric-key encryption?
Which of the following is a primary weakness of asymmetric-key encryption?
Which of the following is necessary for each of the firewalls to allow private IP addresses to be passed on to
What is the primary strength of symmetric-key encryption?
What is the primary strength of symmetric-key encryption?
Which of the following tools is the most appropriate choice?
You have been assigned to provide security measures for your office’s reception area. Although
the company needs to provide security measures, costs must be kept to a minimum. Which of the
following tools is the most appropriate choice?