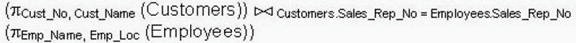
Which of the following SQL statements is equivalent to this relational algebraic expression?
A hash encryption function:
A hash encryption function:
Which line of code will deliver the pop-up window that displays this message?
Consider the following message displayed in a pop-up window: Welcome to the CIW Web site!
Which line of code will deliver the pop-up window that displays this message?
Which XHTML technique does Maria suggest?
Maria and her team are beginning to redesign a corporate Web site. The company owners want to
keep the site’s navigation icons at the top of each page, and enable linked pages to appear in
another section of the same browser window. Which XHTML technique does Maria suggest?
Which of the following describes the goal of a gap analysis?
Which of the following describes the goal of a gap analysis?
Which of the following is the most effective way to respond to this attack?
You have determined that the company Web server has several vulnerabilities, including a buffer
overflow that has resulted in an attack. The Web server uses PHP and has direct connections to
an Oracle database server. It also uses many CGI scripts. Which of the following is the most
effective way to respond to this attack?
What are the MAIN reasons to build use cases?
What are the MAIN reasons to build use cases?
Which two of the following scenarios are better modeled in the JMS point-to-point domain than in the JMS publi
Which two of the following scenarios are better modeled in the JMS point-to-point domain than in
the JMS publish-subscribe domain?
what is one of the functions of the <input> tag?
In XHTML, what is one of the functions of the <input> tag?
Which of the following is true when creating vector masks?
Applying masks in Flash allows for the creation of depth on the Web page. Which of the following
is true when creating vector masks?