What is the key difference between host-based and network-based intrusion prevention?
What is the key difference between host-based and network-based intrusion prevention?
which two statements are true?
Which statement is correct based on the show login command output shown?
Which four methods are used by hackers?
Which four methods are used by hackers? (Choose four.)
Which statement about Cisco IOS IPS on Cisco IOS Release 12.4(11)T and later is true?
Which statement about Cisco IOS IPS on Cisco IOS Release 12.4(11)T and later is true?
Which characteristic is the foundation of Cisco Self-Defending Network technology?
Which characteristic is the foundation of Cisco Self-Defending Network technology?
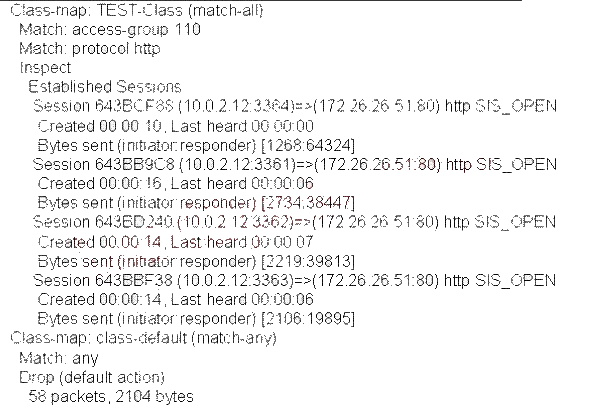
Which kind of table do most firewalls use today to keep track of the connections through the firewall?
Which kind of table do most firewalls use today to keep track of the connections through the firewall?
Which Cisco IOS command is used to verify that either the Cisco IOS image, the configuration files, orboth hav
Which Cisco IOS command is used to verify that either the Cisco IOS image, the configuration files, orboth
have been properly backed up and secured?
What does the secure boot-config global configuration accomplish?
What does the secure boot-config global configuration accomplish?