Which two mechanisms can be used to improve convergence time during a failure?
You are designing a core MPLS-based network with a single OSPF area with no external routes.
Which two mechanisms can be used to improve convergence time during a failure? (Choose two.)
Which three factors slow down network convergence?
Which three factors slow down network convergence? (Choose three.)
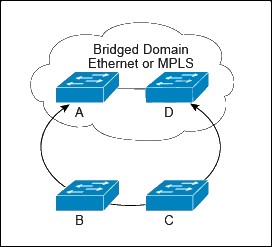
Which two options provide the best loop protection in this topology, regardless of a bridged domain configurat
Which two options are characteristics of firewall transparent mode operations in a firewall solution design?
Which two options are characteristics of firewall transparent mode operations in a firewall solution
design? (Choose two.)
Which two options will accomplish this scenario?
Service Provider A and Service Provider B have agreed to a strategic interconnect relationship
that will allow them access into each other’s geographies by using an inter-AS eBGP VPNv4
multihop between route reflectors. Which two options will accomplish this scenario? (Choose two.)
Which two technologies allow for FCoE via lossless Ethernet or data center bridging?
You have been tasked with designing a data center interconnect as part of business continuity.
You want to use FCoE over this DCI to support synchronous replication. Which two technologies
allow for FCoE via lossless Ethernet or data center bridging? (Choose two.)
Which two interconnect technologies support MACsec?
You have been tasked with designing a data center interconnect to provide business continuity.
You want to encrypt the traffic over the DCI using IEEE 802.1AE MACsec to prevent the
deployment of any firewall or IPS. Which two interconnect technologies support MACsec?
(Choose two.)
Which two options will minimize the impact of the trusted NMS polling your network in this situation?
You need to redesign your NMS system so that it can collect information without causing adverse
effects in the network, such as high CPU utilization on network devices and network instability.
Which two options will minimize the impact of the trusted NMS polling your network in this
situation? (Choose two.)
Which two mechanisms can you use to isolate the data center area from the hub-and-spoke area without losing IP
Which three reasons to deploy an IDS sensor in promiscuous mode when you design a security solution are true?
Which three reasons to deploy an IDS sensor in promiscuous mode when you design a security
solution are true? (Choose three.)