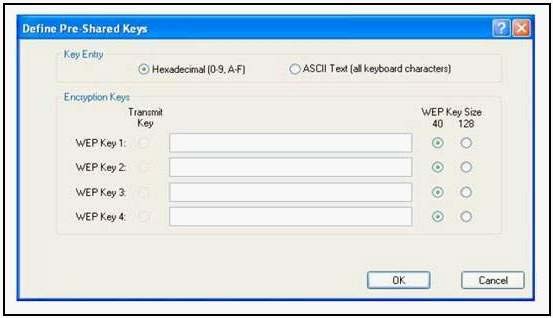
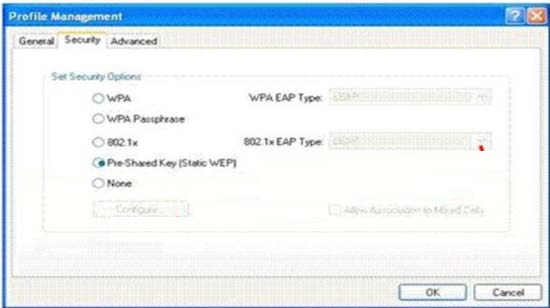
What should be taken into consideration when using the Cisco Aironet Desktop Utility (ADU) to configure the st
What will happen if the access point receives packets sent by the wireless client adapter that are not encrypt
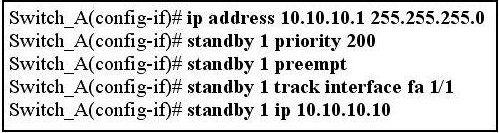
What is the sequence of events when a VoIP call is placed from IP phone P1 to IP phone P2?
Why is BPDU guard an effective way to prevent an unauthorized rogue switch from altering the spanning-tree top
Why is BPDU guard an effective way to prevent an unauthorized rogue switch from altering
the spanning-tree topology of a network?
What two steps can be taken to help prevent VLAN hopping?
What two steps can be taken to help prevent VLAN hopping? (Choose two.)
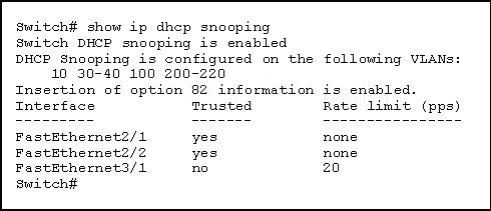
What type of attack would be mitigated by this configuration?
Which statement is true about voice VLANs?
Which statement is true about voice VLANs?
what purpose is the command config network webmode enable used?
For what purpose is the command config network webmode enable used?