Which priority is most important when you plan out access control lists?
Which priority is most important when you plan out access control lists?
Which type of Cisco IOS access control list is identified by 100 to 199 and 2000 to 2699?
Which type of Cisco IOS access control list is identified by 100 to 199 and 2000 to 2699?
Which statement about this debug output is true?
Refer to the below.
14:00:09: TAC+: Opening TCP/IP connection to 192.168.60.15 using source 10.116.0.79
14:00:09: TAC+: Sending TCP/IP packet number 383258052-1 to 192.168.60.15 (AUTHEN/START)
14:00:09: TAC+: Receiving TCP/IP packet number 383258052-2 from 192.168.60.15
14:00:09: TAC+ (383258052): received authen response status = GETUSER
14:00:10: TAC+: send AUTHEN/CONT packet
14:00:10: TAC+: Sending TCP/IP packet number 383258052-3 to 192.168.60.15 (AUTHEN/CONT)
14:00:10: TAC+: Receiving TCP/IP packet number 383258052-4 from 192.168.60.15
14:00:10: TAC+ (383258052): received authen response status = GETPASS
14:00:14: TAC+: send AUTHEN/CONT packet
14:00:14: TAC+: Sending TCP/IP packet number 383258052-5 to 192.168.60.15 (AUTHEN/CONT)
14:00:14: TAC+: Receiving TCP/IP packet number 383258052-6 from 192.168.60.15
14:00:14: TAC+ (383258052): received authen response status = PASS
14:00:14: TAC+: Closing TCP/IP connection to 192.168.60.15
Which statement about this debug output is true?
Which option is a characteristic of the RADIUS protocol?
Which option is a characteristic of the RADIUS protocol?
Which two options are two of the built-in features of IPv6?
Which two options are two of the built-in features of IPv6? (Choose two.)
Which type of security control is defense in depth?
Which type of security control is defense in depth?
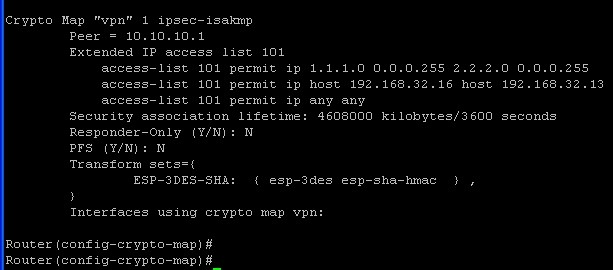
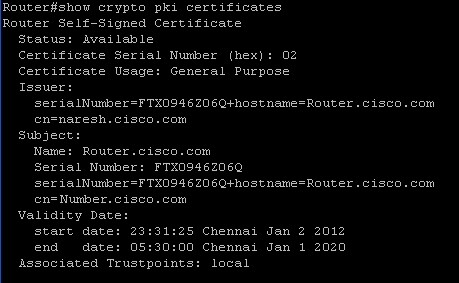
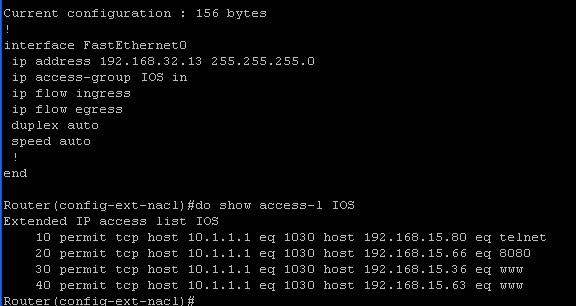
Which three statements about these three show outputs are true?
Which statement describes how the sender of the message is verified when asymmetric encryption is used?
Which statement describes how the sender of the message is verified when asymmetric encryption is used?
Which state must a signature be in before any actions can be taken when an attack matches that signature?
You use Cisco Configuration Professional to enable Cisco IOS IPS. Which state must a signature be in before any actions can be taken when an attack matches that signature?