Which is used to authenticate remote IPsec VPN users?
Which is used to authenticate remote IPsec VPN users?
Which VPN technology is not suitable to be deployed over the Internet?
Which VPN technology is not suitable to be deployed over the Internet?
What are two differences between symmetric and asymmetric encryption algorithms?
What are two differences between symmetric and asymmetric encryption algorithms? (Choose
two.)
What are the four typical design choices to consider when designing Cisco solution-based enterprise remote-acc
What are the four typical design choices to consider when designing Cisco solution-based
enterprise remote-access solutions? (Choose four.)
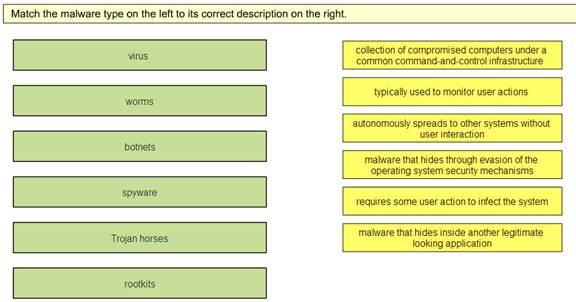
Match the malware type on the left to its correct description on the right.
What is used at the access layer to provide logical separation between the voice and data traffic?
What is used at the access layer to provide logical separation between the voice and data traffic?
Which authentication protocol can provide single sign-on (SSO) services?
Which authentication protocol can provide single sign-on (SSO) services?
Which solution stops new web threats the earliest?
Which solution stops new web threats the earliest?
Which essential element is needed to perform events analysis and correlation?
Which essential element is needed to perform events analysis and correlation?
Which three benefits does DMVPN offer?
Which three benefits does DMVPN offer? (Choose three.)