Which method will always compute the password if it is made up of the character set you selected to test?
Which method will always compute the password if it is made up of the character set you selected
to test?
Which vulnerability is not expected in a network design comprised of multiple security zones, multiple user gr
Which vulnerability is not expected in a network design comprised of multiple security zones,
multiple user groups, and a single physical switch?
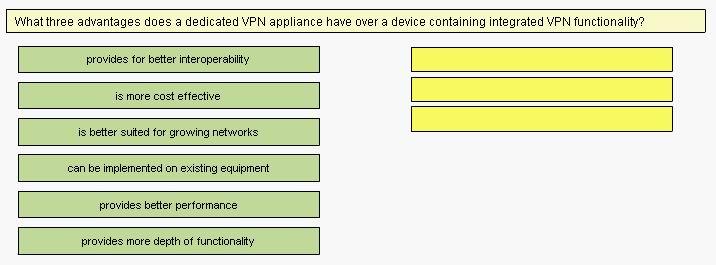
Match three advantages does a dedicated VPN appliance have over a device containing integrated VPN functionali
Which threats are expected in the SAFE Enterprise Network Building Distribution module?
Which threats are expected in the SAFE Enterprise Network Building Distribution module?
(Choose three).
Which two devices in the SAFE SMR small network campus module should have HIDS installed?
Which two devices in the SAFE SMR small network campus module should have HIDS installed?
Choose two.
What are two advantages of using integrated systems and appliances?
What are two advantages of using integrated systems and appliances? Choose two.
What services does EAP provide?
What services does EAP provide?
What are three steps of the Security Wheel?
What are three steps of the Security Wheel? Choose three.
What are the three modules in the SAFE SMR midsize network design?
What are the three modules in the SAFE SMR midsize network design? Choose three.
How are trust exploitation attacks mitigated in the SAFE SMR midize network design corporate Internet module?
How are trust exploitation attacks mitigated in the SAFE SMR midize network design corporate
Internet module?